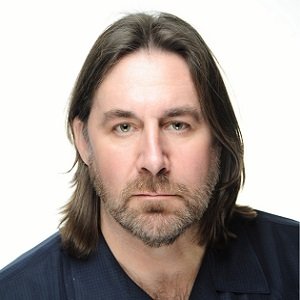
Jeremy Hyatt

Jeremy Hyatt
Director of marketing, HIDNews mentions
Better, faster networking plays into the optimistic outlook for the transportation vertical Our market has plenty of reasons to be optimistic about the future of security systems in...
The security landscape continues to evolve in new, complex ways for transportation customers Dealers looking to enter – or to expand their presence in – the transporta...
Airports, metro systems and other transportation centers must deploy multiple layers of access control for restricted areas Airports, metro systems and other transportation centers...