Hotels, leisure & entertainment security applications - Expert commentary
2016 was a year of fast-paced changes in the market for video surveillance, especially for higher-resolution and panoramic cameras. We spoke with Scott Schafer, Arecont Vision’s Executive Vice President, for his thoughts on 2016 and the year ahead. SourceSecurity.com: Did your predictions for 2016 match up with what you thought back at the end of 2015? How has the intervening year changed the thoughts? Scott Schafer: Looking back on our predictions for industry trends...
There has been a lot of investment in safe city projects around the world in 2016, particularly in India, where Qognify is currently involved in a number of major initiatives, as well as upgrading of security systems at major public transportation hubs and international airports. At Qognify, we have seen a continual trend towards organizations wanting their security systems to deliver operational efficiency and effectiveness to the wider business. Here are some notable trend...
The access control industry is now picking up the challenge of embracing new technologies The access control business has, over the last 10 years, completely changed its image from being a rather unattractive slow growth and conservative business to taking up a position as a fast-growing confident business. The access control industry has listened and acted on the needs of the stakeholders in the supply chain and as a result the world market for access control products and so...
New construction has continued to grow as a result of low interest rates in 2016 and that has positively impacted the security marketplace. Yet the limited availability of skilled labor is becoming a large issue as it leads to higher cost of labor. This also creates a challenge in recruiting, training, and retraining a capable staff in building construction and maintenance activities. As a result, there is a continued desire to improve our efficiency in production, commissioning and the manageme...
The security market in 2016 saw an uptick in the economy, the introduction of new technologies, increased compliance requirements in key verticals, and rising concerns over the need for greater security. Users interested in upgrading or deploying new systems consistently chose networked system platforms. This trend further drove the demand for adaptive transmission solutions as a means of repurposing existing analog infrastructure to accommodate IP devices on a networked platform. As this migr...
Three key trends will continue dominating the security industry looking ahead to 2017 – cloud video, predictive maintenance and emergency preparedness. Cloud Video The continued integration of cloud and hosted video into security programs offers a lot of benefits for customers. The convenience of remotely viewing video footage in real-time or historic footage has been a great benefit to our customers and provides significant business intelligence. It helps with everyt...
There will likely continue to be high numbers of lone wolf and soft target attacks in the year ahead. The drivers behind these tragedies are a confluence of self-radicalization, social media, violent extremism, and mental illness. They will require our skills as security professionals — observation, investigation, interviewing, due diligence — like never before.Looming in the background of these physical attacks is the prospect of combined physical and cyberattacks that could disable...
The single largest group of consumer IoT devices being deployed is for home automation and residential security Business and technology analysts are in unanimous agreement that the number of IoT devices will explode into the many 10’s of billions within the next five years. These billions of new computing devices will produce enormous volumes of data about ourselves, our society, and our physical environment. The security industry is at ground zero of this upheaval. In f...
This executive brief explores the security risks associated with using CSN instead of reading the data protected by security mechanisms. When contactless smart cards are implemented and deployed properly, they represent one of the most secure identification technologies available. However, some manufacturers, in an attempt to sell a ‘universal’ reader capable of reading almost any contactless smart card technology, actually disable the built-in security...
Thermal cameras see heat rather than light, so they are a perfect “human detector” Safeguarding outdoor assets in a reliable and cost-effective manner often comes down to a single requirement: Accurate intruder alerts and timely information about the unfolding event. While there are many technologies available for outdoor security, smart cameras with video analytics have emerged as the solution of choice for detecting intruders in real time outdoors. Yet the best...
Vulnerability scans rely on mostly automated tools to find potential vulnerabilities at either the network or application level Security vulnerability in any network can be found and exploited by hackers and others in no time. The only questions are when this will happen and how much damage an individual could do once they’ve gained access to the network. Recognizing this reality, most organizations test their own networks for security weaknesses, whether to meet compli...
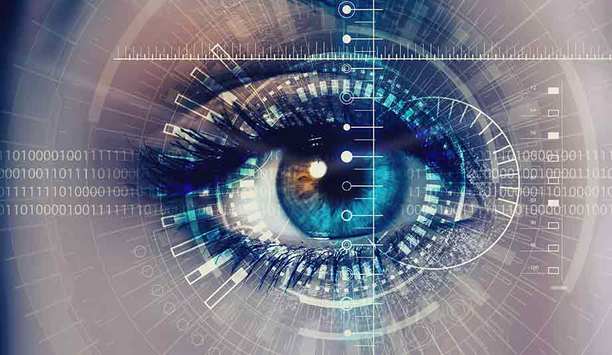
Iris recognition measures the unique patterns in the coloured portion of the eye (the iris) and compares that ‘signature’ to the one on file Since the late 1990s, iris recognition technology has been used in banks and airports as a means of identity authentication. Today, its use is widespread in government facilities, schools/research centers, correctional/judicial facilities, healthcare and others. There are a number of reasons for its rising popularity, but firs...
Currently some retailers operate two separate speaker systems in their stores: one for broadcasting background music and one for announcements Twenty years ago, IP network cameras launched a revolution in video surveillance. Today, network audio systems are about to do the same for the speaker market. Back in 1996, the predominant video cameras were analog. They weren’t intelligent. They required an expensive and complex head-end of recording and monitoring systems. An...
As the trend from analog to IP continues to progress, more and more security devices are IP-enabled for seamless network integration With rising concerns over organizations’ physical security and potential network vulnerabilities, it has become more important now than ever for security professionals and other decision makers to take actions that will guard against potential problems and help prevent system failures. One specific area of heightened focus is the implementa...
If all the components within a security and wider IT network have the ability to interact together, they can offer so much more than their individual capabilities The widespread use of open protocol systems is one of the most important developments in the security and safety sector for decades. With a heavy reliance upon various security softwares (even for physical security), using open systems has gone from being a desirable selling point to a necessity in the security indus...
Multi-modal biometrics refers to a technology that combines a number of biometrics working together as a multifactor solution Global terrorism is on the rise. For many years, the West felt immune to these incidents, often asserting that these were problems felt only in countries with heated conflicts, such as Syria, Iraq, Israel and Nigeria. However, recent terror attacks have taken place in both Europe and the United States: Belgium, France (Paris and Nice), Orlando, various...
Panoramic cameras enable an operator to assess a wide field of view at a glance and to zoom in to view additional detail as needed. Providing this capability are a single camera, a single mounting location, and often using a single cable. Complete 180-degree or 360-degree coverage brings total situational awareness of the area being viewed. Panoramic cameras can also enable you to record everything in the field of view, all the time, and to zoom in for detail, wheth...
Access levels of individuals based on their roles can be cross compared with their normal access patterns, it is also useful to look for anomalies in device behavior Threats to an organization’s physical and logical security are increasing in number and financial impact, according to several recent surveys. To combat this problem, security and IT professionals are fighting back with system upgrades and software solutions including advanced analytics. Using the analytics...
The technologies behind physical access control are constantly evolving. It’s a fast-changing market that can leave end user organizations struggling to keep up. Smart cards still reign supreme, with good reason, but there are also new options today and on the horizon. Customers want to implement the most secure and up-to-date technologies, but constantly adapting their systems to keep up with the pace of change is impractical. Leveraging access control technologies in a way that both m...
The global market for security as a service is set to grow from $921 million in 2016 to $1.49 billion by 2020 The global security as a service market is made up of video surveillance as a service (VSaaS) and access control as a service (ACaaS). With video surveillance as a service, the user pays on a yearly, quarterly or monthly basis for the ability to view live or recorded surveillance data. Using access control as a service, the customer pays a subscription to have a server...
Keen Yao responds to reports around Hikvision's ties to the Chinese state, and its role as the biggest video surveillance equipment manufacturer in the world Hikvision has been in the news in the United Kingdom recently, including a front page news story in The Times. SourceSecurity.com offered Keen Yao, Vice President at Hikvision’s International Business Centre, a chance to set the record straight regarding concerns expressed about hacking of cameras, the company&rsquo...
IP/PoE systems eliminate the need for local power, thus saving installation costs Cost considerations are an important reason to use existing installed cable as part of a new system infrastructure. Extenders in the form of media converters can help. For almost three decades, video surveillance systems existed in the form of analog systems. Video coaxial cable was the primary method of transmission with a limited distance of about 750 feet. Analog systems required separate pow...
When a manufacturer states a specific PoE power for a camera, always count on the maximum class power source Power over Ethernet (PoE) is an important consideration in IP video security infrastructures, and many people believe Institute of Electrical and Electronics Engineers (IEEE) standards are the last word. However, when it comes to PoE, there is a wide range of both voltages and wattages that can qualify as being within an individual IEEE power class. This applies to both...
Features such as height-adjustable tabletops and adjustable monitor options can fine-tune the workstation The security market is one of the most demanding AV applications. Each environment in the security field presents its own unique set of challenges and requirements that revolve around advanced AV systems and the operators that utilize them. For monitoring and control room operators, that means continuous vigilance with little to no downtime away from their stations. Becau...
If you want to cultivate new ideas among your employees, it is important to let them know that they are allowed to challenge the status quo The Americans asked for horses – Henry Ford gave them cars. In the beginning of the 20th century, he disrupted the transportation industry. He created a new market outmatching established leading companies, products and alliances. And he got the idea himself. Many of us want to disrupt our industries with new innovations that...
The use of multiple wires has advantages for network transmission Network connection to a remote device begins by considering the type of cable. In some cases, installed cable may already be present and available for reuse, or you may have the option to install a new cable. Let’s review the major types of cable used for most security applications, their advantages and disadvantages. Types Of Cables In general, there are four major types of cable. First is coaxial cab...
The Hugs Infant Protection Solution tracks the location of babies and provides protection anywhere the infant may be transported Wireless tracking and radio frequency identification (RFID) continue to improve dramatically in range and reliability, allowing Real-Time Location Systems (RTLS) pinpointing people, places and things with impressive accuracy. Systems integrator Advance Technology Inc. (ATI), Scarborough, Maine, recently installed a comprehensive, hospital-wide soluti...
Deploying audio solutions would flag incidents not caught on camera With the increasing number of campus shootings and lockdowns, security is a top priority for schools. Decision-makers are looking to repair the inefficient security measures on campuses by either upgrading their current systems or installing state-of-the-art technologies to enhance situational awareness. Traditionally, security personnel have relied on video as the primary method of monitoring. However, this...
48% of U.S. judges say they are not adequately prepared to deal with the range of “scientific or technical evidence” presented in court Over the last decade, the video surveillance security industry has morphed drastically in attempts to keep pace with both the consumer electronics and enterprise IT markets. This has created a steep learning curve for law enforcement as well as individuals in the judicial system. A 2012 survey titled “A national survey of ju...
The field of artificial intelligence known as machine learning or cognitive computing has in recent years become highly popular The field of artificial intelligence known as machine learning or cognitive computing has in recent years become highly popular. The meteoric rise of “deep learning” technology over the past several years has been truly dramatic in many industries. Industry giants from Google, Microsoft, Facebook, IBM and many others have been pouring mass...