Mobile access articles
It’s hard to believe that we’re in the final quarter of 2019. It’s time to wrap up goals and make new ones that will guide us into another decade. As we look forward, we can’t help but look back at some of the key trends that emerged in the last couple of years, and their continued presence in the product road maps and plans that so many security industry leaders and manufacturers are creating. Some of these trends have enhanced the efficacy of security systems, wh...
The statistics are staggering. The death tolls are rising. And those who now fear environments that were once thought to be safe zones like school campuses, factories, commercial businesses and government facilities, find themselves having to add the routine of active-shooter drills into their traditional fire drill protocols. The latest active shooter statistics released by the FBI earlier this year in their annual active-shooter report designated 27 events as active shooter incidents in 2018...
With the recent news headlines about store closures and the collapse of well-known chains, alongside clear adjustments in business strategy amongst established high street favorites, there is no denying that the UK retail industry is under huge pressure. A recent report suggests growing issues are leading some retailers to increase risk-taking in the supply chain. But here, Steve Bumphrey, Traka UK Sales Director, looks at ways to help retailers embrace the storm, including paying attention to...
Airport environments have become more sophisticated and complex over the course of the last 20 years. What was once a simple structure to facilitate travel from point A to point B has now been transformed into a hustling and bustling setting that offers passengers the comforts and conveniences of a small city. As a result, the complexity of risks that airport operators face has grown exponentially. Security personnel must now mitigate risks like terrorism, theft, personal safety and insider thr...
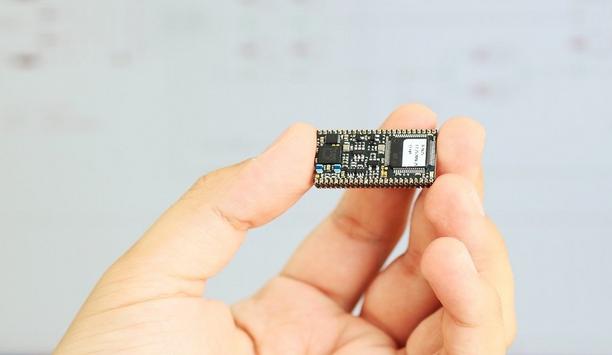
Edge devices (and edge computing) are the future. Although, this does seem a little cliché, it is the truth. The edge computing industry is growing as quickly as technology can support it and it looks like we will need it to. IoT Global Market The IoT (Internet of Things) industry alone will have put 15 billion new IoT devices into operation by the year 2020 according to a recent Forbes article titled, “10 Charts That Will Challenge Your Perspective of IoT’s growth”. I...
The industry faces numerous challenges in the coming year. Physical and cyber security threats continue to become more complex, and organizations are struggling to manage both physical and digital credentials as well as a rapidly growing number of connected endpoints in the Internet of Things (IoT). We are witnessing the collision of the enterprise with the IoT, and organizations now must establish trust and validate the identity of people as well as ‘things’ in an environment of in...
It’s not surprising that people are nervous about the security of newer technologies, many of which are part of the Internet of Things (IoT). While they offer greater efficiency and connectivity, some people still hesitate. After all, there seems to be a constant stream of news stories about multinational corporations being breached or hackers taking control of smart home devices. Both of these scenarios can feel personal. No one likes the idea of their data falling into criminal hands. A...
With the coming of a New Year, we know these things to be certain: death, taxes, and… security breaches. No doubt, some of you are making personal resolutions to improve your physical and financial health. But what about your organization’s web and mobile application security? Any set of New Year’s resolutions is incomplete without plans for protecting some of the most important customer touch points you have — web and mobile apps. Every year, data breaches grow in scop...
Market dynamics are changing the U.S. residential security market, creating new business models that better appeal to the approximately 70% of households without a security system. Smart home adjacencies have helped revitalize the traditional security industry, and alternative approaches to systems and monitoring for the security industry are emerging, including a new batch of DIY systems. Growth in the residential security market and its position as the channel for smart home solutions have at...
Whether you are a veteran in the access control world or have never installed a card reader before, there are always ways to increase profits in the ever-evolving world of access control. The hope is that by considering a few key focal points, you can find ways to increase market share. Whether we are releasing an electronic lock through a simple intercom button or using biometric and multi-authentication based on a database; the tactics for bringing on more revenue is the same. Learning to focu...
Facial recognition has a long history dating back to the 1800s. To track down criminals, such as infamous bandits Jesse Woodson James and Billy the Kid, law enforcement would place “Wanted Alive or Dead” posters advertising bounties and soliciting public cooperation to help locate and even apprehend the alleged criminals. In addition to the bounty, these posters would include a photo and brief description of the crime, which would then be circulated to law enforcement agencies arou...
Considering how much the modern smartphone has become a common everyday tool and cultural icon, it’s hard to believe it has only been with us for a relatively short space of time. The first Apple iPhone was launched in 2007 and yet in a little over a decade the smartphone has become as essential as our keys or wallet. From its conception as a multi-faceted communications device, it has morphed into something far more integrated in our daily lives. Services such as Apple Pay, Android Pay a...
For the past several years, there has been a focus by integrators and customers to assure that their card-based access control systems are secure. To give businesses an extra incentive to meet their cybersecurity threats, the Federal Trade Commission (FTC) has decided to hold the business community responsible for failing to implement good cybersecurity practices and is now filing lawsuits against those that don't. For instance, the FTC filed a lawsuit against D-Link and its U.S. subsidiary, al...
Artificial intelligence and machine learning are the rage in tech right now and not surprisingly, many cyber companies are beginning to automate an increasing amount of their operations. Some of this is great, particularly when it assists cybersecurity professionals to automate mundane tasks and focus more of their attention on higher level analysis. But so far, machine learning is more hype than helpful for cybersecurity, but that does not mean you can’t automate some tasks to keep your...
Schools today are charged to provide an environment that is both safe and conducive to learning, which can be difficult considering the range of security incidents and challenges they face, including bullying, fights, graffiti, theft and more. In addition to working within often tight budgetary constraints, a main challenge is to provide the highest level of security in an aesthetically pleasing way that doesn’t make students feel as if they are in prison. While these two needs may seem...
Small business owners work hard. They are often the first ones there in the morning and the last to leave at night. Even then, they likely bring their work home with them. During that time, everything they do is aimed at making their business as successful as possible. Because of this, many business owners don’t take vacations, and if they do, they spend a lot of time worrying about their business while they’re away. In both cases, the potential for burnout is tremendously high. Th...
Until recently, the convenience and security of “smart” electronic locks have been exclusively enjoyed by owners of homes, with renters largely being left out in the cold. Locked out by the temporary nature of their living arrangement, and not allowed to make structural changes to their temporary abodes, these renters have been unable to enjoy the many benefits of these connected devices. But today, smart lock capabilities are becoming available to renters and rental property owners...
Most cities have at very least a plan and in most cases an existing program to make themselves safe cities. Increasingly, cities around the world are transitioning to become smart cities: urban areas where security solutions work in unison with other systems, extending the benefits of technology beyond security and into other city operations. While this transformation has yet to become a widespread the next crucial transition—from smart city to cognitive city—is already appearing o...
2017 was an incredible year for VuTeur and the industry as a whole, as security has become a primary focus for stakeholders, now more than ever. VuTeur introduced its proprietary IRIS (Internal Real-time Intelligence Software) technology this year, which is part of its emergency management and asset protection solution. IRIS leverages real-time location services (RTLS) technology and utilizes the existing WiFi infrastructure in a building to create a personal, mobile safety...
In 2017, SALTO Systems led the market with increased emphasis on two growing sectors within access control: Mobile technology and cloud solutions. Strengthening Market Positions Mobile access control applications are now a must across all security verticals. The hospitality sector, for example, is quickly seeing smartphones replacing room keys and check-in lines with mobile apps like SALTO’s JustIN Mobile. This technology replaces the need for an access card by securely sending a mobile...
In 2017, access control solutions evolved and expanded within physical security operations, aligning with the overall industry trend of moving security from a reactive to a more proactive model. Access Control Serving The Industry From increased integration capabilities to mobile applications to predictive analytics, access control served as the platform that enabled this transition in physical and data security. Other steady growth areas included wireless readers, smartphone usage as a crede...
Overall, it’s been quite a year for the industry and Vanderbilt. Last year, we predicted that the security industry would see a rise in cloud-based systems in 2017, and based on the developments and trends we've seen over the last 12 months, that forecast has come true. ACT365 Access Control And VMS Vanderbilt introduced the ACT365 cloud-based access control and video management solution to its portfolio, and it has plans to educate the marketplace on the technological and economic advan...