Healthcare articles
Video surveillance as a service (VSaaS) is not just for commercial organisations. Federal, state and local governments can also realize benefits from the technology—and use it to deliver an integrated video surveillance system that addresses some of their unique security needs. Video Surveillance as a Service (VSaaS) What is VSaaS? Simply stated, it’s a cloud-based video surveillance solution that is packaged and delivered as a service over the internet. The price varies depending...
2017 was an incredible year for VuTeur and the industry as a whole, as security has become a primary focus for stakeholders, now more than ever. VuTeur introduced its proprietary IRIS (Internal Real-time Intelligence Software) technology this year, which is part of its emergency management and asset protection solution. IRIS leverages real-time location services (RTLS) technology and utilizes the existing WiFi infrastructure in a building to create a personal, mobile safety...
In the wake of Securing New Ground event in New York City in 2016, the Security Industry Association (SIA) published an inaugural “Security Megatrends” report that assessed for major “megatrends” for the security industry in 2017. 10 Major Megatrends Only days ago, SIA published “Security Megatrends: The 2018 Vision for the Security Industry,” again identifying 10 major megatrends to watch in the year ahead. SIA saw a great deal of activity unfold in 2017, a...
Throughout 2017, customers have been increasingly looking for technological answers to a plethora of their business needs, and the surveillance industry has seen a rapid boost because of this. In particular, we’ve seen more organizations harness video to fulfill much more than just their security requirements. Combining Physical And Cyber Security Businesses are now using surveillance to address areas such as health and safety, sales and marketing as it fast becomes more of a business op...
The security industry remains interested in capturing actionable data from video analytics and this year we saw increasing interest from non-security industries. While still a relatively young industry for our market—think of where Google was with collecting metadata 10 years ago—video security works with similar algorithms for capturing various scenarios. The data this provides is becoming more valuable not only for security purposes, but also for business operations, such as deter...
Biometric identification technologies today are becoming pervasive. Many smartphones offer fingerprint unlock options, and most organizations have at least considered the technology as a solution for their identification and access needs. While biometrics have dramatically improved in the past several years to deliver faster, more efficient and more secure solutions, not everyone is ready for the change. New York MTA Case Study But does that mean that organizations need to hold off on implemen...
There have been many changes in the healthcare environment over the past decade. The Affordable Care Act has been established, severe weather events are on the rise, violence along with active shootings continue to increase, behavioral health patients present treatment challenges and hospitals continue to consolidate to increase purchasing and service capabilities. Over the next decade, healthcare will continue to transform. Emphasis will be on financial reform, violence response, emergency prep...
There has never been closer integration between physical and logical security systems, so there has also never been greater importance when it comes to defining and maintaining the security culture within an organization. Unfortunately, with increasingly complex security protocols required on a daily basis (and used by every employee), a security regime can easily become lax through apathy – which offers the perfect opportunity for potential intruders to take advantage. While securi...
Robots have been in the spotlight lately, as tycoons like Elon Musk discuss the perils of automation and artificial intelligence (AI), and roving robots meet their watery demise. These recent events have unmasked a particularly interesting topic: The value of robots in the broader sense, especially as a security tool. The emergence of robotics, automation and AI is not new, but the ongoing discussion about how best to use these continues to fuel critics and supporters alike. Seattle-Tacoma Inte...
Real-time location systems allow organizations to communicate with visitors, employees, and staff in the event of an emergency Today's threat landscape is bigger and more broad than ever before, with an increasing number of emerging risks falling on the shoulders of security professionals in a variety of markets. Many of these leaders face the growing concerns of finding efficient, integrated solutions that provide protection from threats, but also can be used in everyday comm...
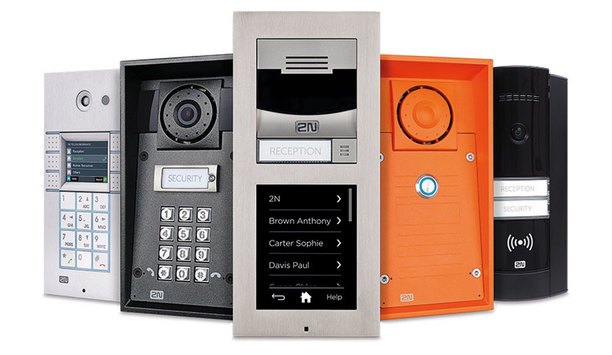
Part 1 in our Intercoms in Security Series Lambert-St. Louis International Airport uses Code Blue intercoms Organizations are demanding a new level of interoperability among mission-critical security systems. Intelligible audio, the ability to hear, be heard and be understood, is critical to communication, which is essential to the core security processes within an organization, as well as to emergency situations. Intelligible audio provides a platform to optimize v...
Part 2 of our Intercoms in Security Series The 2N Helios IP family intercoms present a comprehensive portfolio of security offerings for businesses and individuals Some integrators and end users may think of intercoms as older technology that isn’t required as part of a robust security system. Not true. Intercoms include innovative technologies that have developed rapidly, keeping pace with other categories. Just as cameras and access control systems have made techn...
It is critical to be able to clearly outline the end user’s potential return on investment Smart buildings are on the rise around the world, not only because a growing number of companies are considering their environmental impact, but also because of the dramatic cost savings that can be realized through integration. In every building that has an integrated security and access control system, an opportunity awaits to also integrate the building’s energy use, water...
Organizations are moving to align their physical and digital security initiatives, especially in today’s more connected world Organizations must address growing security threats using fewer resources in an increasingly challenging regulatory environment. They are looking to ensure data security while also protecting their facilities’ physical security. At the same time, their users are demanding more choices of smart cards, smartphones, wearables, and other mobile...
The top influencing trends in the security industry at ISC West 2017 will be big data, cyber security and the Internet of Things More than a thousand companies will be showing off their latest and greatest technologies and services at this year’s ISC West in Las Vegas. With so much to look at and experience, will you be able to pinpoint the next big thing or things that will dominate the security market in 2017? A good way to predict those upcoming trends is to look at w...
Through new technology, applications and analytics, video surveillance systems are helping to make hospitals a safer place Healthcare organizations face many challenges. Federal mandates associated with the Affordable Care Act (ACA), changing reimbursement models, an ageing population and competition are among the most concerning issues. Unfortunately, so are safety and security. However, video surveillance is helping. Through new technology, applications and analytics, v...
Three key trends will continue dominating the security industry looking ahead to 2017 – cloud video, predictive maintenance and emergency preparedness. Cloud Video The continued integration of cloud and hosted video into security programs offers a lot of benefits for customers. The convenience of remotely viewing video footage in real-time or historic footage has been a great benefit to our customers and provides significant business intelligence. It helps with everyt...
Iris recognition measures the unique patterns in the coloured portion of the eye (the iris) and compares that ‘signature’ to the one on file Since the late 1990s, iris recognition technology has been used in banks and airports as a means of identity authentication. Today, its use is widespread in government facilities, schools/research centers, correctional/judicial facilities, healthcare and others. There are a number of reasons for its rising popularity, but firs...
If all the components within a security and wider IT network have the ability to interact together, they can offer so much more than their individual capabilities The widespread use of open protocol systems is one of the most important developments in the security and safety sector for decades. With a heavy reliance upon various security softwares (even for physical security), using open systems has gone from being a desirable selling point to a necessity in the security indus...
Part 11 of our Security in Healthcare series The Joint Commission’s mission is to continuously improve health care for the public, in collaboration with other stakeholders Compliance with Joint Commission accreditation can impact hospital and healthcare safety and security decisions, and can even drive security system improvements at healthcare facilities. An independent, not-for-profit organization, The Joint Commission accredits and certifies nearly 21...
The age of robotics is fast approaching. To be successful, security systems integrators need to understand how these machines fit in the security of their clients, according to industry experts. “The integrators did not begin this trend,” says Bill Bozeman, President and CEO of the PSA Security Network, cooperative of security product suppliers and system integration companies. “They did not say, ‘Oh boy I can’t wait to introduce robotics into my portfolio'. This i...
Part 8 of our healthcare series Hospitals are challenging environments. A hospital requires oversight 24 hours a day, seven days a week Access control in particular has advanced significantly to offer healthcare facilities the ability to control access remotely, through mobile applications, confirm identity quickly and easily and program varying levels of access for visitors, patients, doctors and staff. Hospitals are challenging environments. A hospital requires ov...
Part 7 of our healthcare series Integrators can sell a breadth of possible equipment into the healthcare market One appeal of the healthcare market for North Carolina Sound, an integrator covering central North Carolina, is the breadth of possible equipment they can sell into the healthcare market, including access control and video, of course, but also other technologies, such as audio-video systems in a dining room. North Carolina Sound has also installed sound mask...
Part 5 of our Security in Healthcare series It’s difficult for hospital security directors to provide a quantified ROI in an updated security system Several forces are working in favour of greater adoption of hospital security and video surveillance technologies in the healthcare market. “Healthcare facilities and campuses are growing at a rapid rate to accommodate an aging population and the research and development of pharmacology and many different type...
Part 3 of our Security in Healthcare series Megapixel and higher-definition cameras are meeting the security and surveillance needs of a variety of hospital and healthcare facilities Video is a major component of most hospital and healthcare security systems. Among the big video trends are greater integration of video with other systems, and increased use of higher-megapixel cameras and 180-degree and 360-degree-view cameras to monitor larger areas. Variety Of Video...
What factors should an end user consider when looking for a professional systems solution provider? Andrew Schonzeit, President of IDESCO Corp., New York, knows what it takes to have an award-winning, top-in-its class systems integration company. For more than seven decades, the company has grown, morphed and continued to move into the world of value-add integrated solutions contracting. They’ve received numerous industry and business accolades and increased their statur...
Part 2 of our Security in Healthcare series Users need to be able to upgrade in a way that fits with both their securityneeds and their budgetary limitations The future is digital, and analog systems are a thing of the past – or are they? The fact is, in the healthcare vertical at least, we may still have a way to go before the full potential of IP-based systems is realized. Obstacles include a lack of funding and the challenge of sharing IP bandwidth wi...
Part 1 of our Security in Healthcare series Hospitals have a continuous need for security, to update their systems,and to make repairs The healthcare vertical provides plenty of opportunities for security integrator companies. A single large hospital system can supply a dependable ongoing source of revenue to integrator companies, says David Alessandrini, Vice President, Pasek Corp., an integrator. Hospitals have a continuous need for security, to update their...
ASSA ABLOY door handles with built in reader, strike, request-to-exit sensorand door contacts help maintain sterile environment of stainless steel rooms Access control technology has been around for a long time, but security professionals still run into weird problems when designing and installing systems. For example, when a hospital discovered that it was losing $4,000 per patient bed annually in medicines and other supplies, it asked ASSA ABLOY for an access control solutio...
Temperature, dusty and dirty conditions, along with limited access to networkingmakes remote location video surveillance extremely challenging Properly conducting video surveillance for any organization comes with several challenges. Not the least of which is how to architect a system that finds the right balance between quality, cost and bandwidth impact. This becomes even more challenging in non-traditional, demanding environments that are uncontrolled or highly dispersed, w...