Door access control - Expert commentary
Security and systems integrators across the nation are recommending and providing long-term security solutions to their customers. But when it comes to physical security entrances, integrators can easily fall into the trap of simply fulfilling an end user’s exact request without much pushback. Why? We believe the complexity and variety of entrances available makes it difficult to consult on the best solution, but also because there are a lot of assumptions at play. 1) Ask Questions To De...
Recent developments in physical security systems have enabled us to expand access control using IT infrastructure. By eliminating the need for hard wiring to a central panel or controller, IP-based systems enable installations that are non-proprietary, flexible and scalable. This means not only a more versatile solution, but also a more cost-efficient one. A network-based system can be enlarged by one door, and one reader, at a time, unlike some traditional systems where controllers or panels o...
Securing potentially hazardous sites, which contain gas or oil storage facilities, is becoming increasingly important to UK industry. While other businesses are investing in enhanced access control solutions, such as electronic key-centric access management, many sites containing hazardous materials are left stuck in the dark ages, with basic and impractical mechanical locking systems. This is due to the potential risks associated with using an electronic device, which could cause a spark, in cl...
Since the introduction of smartphones with downloadable applications, vendors have been trying to replace the traditional plastic identification (ID) card with a mobile phone application. People might lose or misplace an ID card, but most people immediately recognize if they are without their mobile phone. Mobile ID badges for access control Bluetooth Low Energy iBeacon technology Technical challenges The logical extension is to replace or augment the traditional corporate ID and access...
Mobile access is probably the largest emerging trend in the security marketplace, but it is only one of several that are changing the face of the access control market. Another factor showing potential to change the market is the emergence of location systems and positioning systems, as reflected by HID Global’s recent acquisition of Bluvision, a provider of real-time location tracking system for assets and employees, and building information modeling (BIM) is impacting how consultants do...
Security consultants are on the front lines of trends such as “smart buildings” and the increasing demand for green technologies. We recently gathered together several consultants to reflect on what’s new in these areas, joined by a representative of HID Global. Participants were Chris Grniet of Guidepost Solutions, Brandon Frazier of Elert & Associates, Terry Harless of Burns & McDonnell, and Harm Radstaak, HID Global’s Vice President and Managing Director, Phy...
The transition from analog to IP technologies has had a large impact on the ways intercoms are used in the security industry. The analog-to-IP transition has generated a lot of attention in the camera market, and the transition is also taking place for intercoms. Twenty years ago, Axis Communications (2N’s parent company) led the industry in converting from analog cameras and video to IP. Integrated IP System The conversion took 15 years to achieve, but the same conversion in intercoms i...
Part 4 in our Intercoms in Security Series The ONVIF standard makes it simple to integrate the intercom with other ONVIF-compliant video management systems, access control solutions, and cameras Open standards are enabling new capabilities in the intercom market, some of it driven by the transition to systems based on Internet protocol (IP). Today’s most-used phrase in the intercom business is interoperability, given that the intercom is integrated with solutions s...
Part 3 of our Intercoms in Security Series: Zenitel’s Call Access Panel manages intelligible critical communications through a security operations center or control room Greater connectivity, security software enhancements, more customization, and better sound quality are some of the enhancements driving the intercom market.An advantage now offered on Code Blue’s emergency speakerphones include self-diagnosing software that monitors the status of the phones an...
Part 1 in our Intercoms in Security Series Lambert-St. Louis International Airport uses Code Blue intercoms Organizations are demanding a new level of interoperability among mission-critical security systems. Intelligible audio, the ability to hear, be heard and be understood, is critical to communication, which is essential to the core security processes within an organization, as well as to emergency situations. Intelligible audio provides a platform to optimize v...
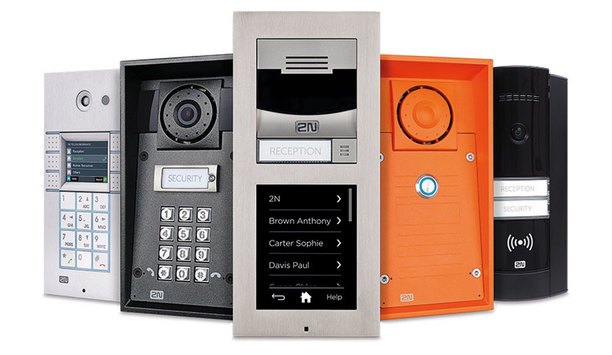
Part 2 of our Intercoms in Security Series The 2N Helios IP family intercoms present a comprehensive portfolio of security offerings for businesses and individuals Some integrators and end users may think of intercoms as older technology that isn’t required as part of a robust security system. Not true. Intercoms include innovative technologies that have developed rapidly, keeping pace with other categories. Just as cameras and access control systems have made techn...
The global market for card-based electronic access control (EAC) is projected to reach $10.1 billion by 2020 according to Global Industry Analysts. However, as credential technologies have evolved over the years, so have the ways users interact with them. Mobile Credentials One of the bigger developments over the past few years has been the increased adoption of mobile credentials, which allows users to access facilities via their mobile device....
Organizations are moving to align their physical and digital security initiatives, especially in today’s more connected world Organizations must address growing security threats using fewer resources in an increasingly challenging regulatory environment. They are looking to ensure data security while also protecting their facilities’ physical security. At the same time, their users are demanding more choices of smart cards, smartphones, wearables, and other mobile...
Smartphones offer a new alternative to traditional physical access control form factors such as smart cards or fobs. Convenience is the most obvious benefit, but there are others. Here are some advantages of using smart devices for access control: 1. Less vulnerability to cloning when compared to magstripe or low-frequency proximity cards. Digital credentials and mobile IDs are securely stored and protected. 2. Longer-distance communication, which allows readers to be mount...
Cultural and hospitality venues are attractive targets for terrorists due to their public accessibility Over the past 40 years there have been numerous attacks carried out against cultural and hospitality venues in the furtherance of religious, ideological, criminal or political beliefs. By default, cultural and hospitality venues are attractive targets for terrorists due to their public accessibility, the volumes of visitors and guests or because of what the venue represents;...
Customers are increasingly requesting both mechanical and electronic services for their doors In most buildings, security is a hybrid solution of both mechanical and electronic security products. Locksmiths take care of the mechanical door hardware and the integrators focus on the electronic security technology. However, for consumers, this traditional division of labor means they must deal with two different companies for the same door - one to design, install and service al...
Physical access control has been a key component of many organizations’ security strategies for several decades. Like any technology, access control has evolved over the years, and solutions now offer more security and convenience than ever before. From swipe technologies, such as the now antiquated magnetic stripe, to a variety of contactless technologies and mobile access credentials, businesses now have several choices when it comes to access control. Upgrading Outd...
Predicting where or how security access trends would develop in 2016 was an educated guess at best. We did, however, forecast continued growth in the areas of wireless readers; smartphone usage as a credential; and more migration to web-based software/hardware solutions.In hindsight, we were not so far off the mark. Wireless security systems proved to be a growing option for extending an access control system and a practical solution for retrofits. Smart phone credentials gained popularity by fr...
After two decades of advances from simple visual ID badges to smart cards, standards-based access control systems and mobile ID solutions, the industry began entering its next new chapter in 2016. We began “mobilizing” security to make it more pervasive and personalized, with a better user experience. We entered a new era of secure connected identities will not only make us safer but fuel innovation in how we work, shop and play. The industry began paying much closer attention to p...
The shift from wired to wireless access control was expected to gather pace in 2016—and that has happened. This year we at Assa Abloy surveyed a large cross-section of security professionals, seeking their insight into the changing market. Comparing our data with research we did in 2014 showed a clear trend towards wireless access control. Wireless Access Data Our 2014 survey found 23% of commercial properties using a wireless or hybrid wired/wireless access control s...
The winds of change have swept into the access control market in 2016. The hardware is transitioning away from being solely panel-based, software is rapidly moving to the cloud, and credentials are going mobile. It seems that the security access control world is finally waking up from its technological slumber, and 2017 will be an exciting time. These three major trends are feeding off one another and are driving the growth all around. IP And Edge Based SystemsIn 2016, hardware companies like...
All access information can be stored and managed by highly trained professionals operating from a remote operations center The security and safety industry has seen tremendous advances in cloud-based access control recently as cloud computing has opened up a world of possibilities for security and access control. Whether controlling access for a single door or for an entire enterprise spread out over multiple locations, cloud-based hosted or managed solutions allow security de...
The technologies behind physical access control are constantly evolving. It’s a fast-changing market that can leave end user organizations struggling to keep up. Smart cards still reign supreme, with good reason, but there are also new options today and on the horizon. Customers want to implement the most secure and up-to-date technologies, but constantly adapting their systems to keep up with the pace of change is impractical. Leveraging access control technologies in a way that both m...
Part 11 of our Security in Healthcare series The Joint Commission’s mission is to continuously improve health care for the public, in collaboration with other stakeholders Compliance with Joint Commission accreditation can impact hospital and healthcare safety and security decisions, and can even drive security system improvements at healthcare facilities. An independent, not-for-profit organization, The Joint Commission accredits and certifies nearly 21...
The Hugs Infant Protection Solution tracks the location of babies and provides protection anywhere the infant may be transported Wireless tracking and radio frequency identification (RFID) continue to improve dramatically in range and reliability, allowing Real-Time Location Systems (RTLS) pinpointing people, places and things with impressive accuracy. Systems integrator Advance Technology Inc. (ATI), Scarborough, Maine, recently installed a comprehensive, hospital-wide soluti...
Part 10 of our Security in Healthcare series Ensuring the safety of patients, staff and visitors is no easy task Security integration is more than a buzzword in the hospital and healthcare vertical. Increasingly, it’s a necessity. When creating a safe and secure healthcare environment, end users should look for solutions that not only drive new levels of security and business intelligence but can provide long-term value in the future. Specifically, Kevin...
The security industry as a whole is migrating from the historical mechanical lock to the newest technology of electronic locks Mechanical locks and keys date back thousands of years and have undergone many changes, but the industry’s transition to electronic locks might be the most important, lasting, and surprisingly affordable security and safety change of all. The objective behind the creation of locks so long ago remains: to control a value on the other side...
Part 8 of our healthcare series Hospitals are challenging environments. A hospital requires oversight 24 hours a day, seven days a week Access control in particular has advanced significantly to offer healthcare facilities the ability to control access remotely, through mobile applications, confirm identity quickly and easily and program varying levels of access for visitors, patients, doctors and staff. Hospitals are challenging environments. A hospital requires ov...
It’s become a hot topic lately, but what are the real prospects for the smart home and home automation market? More specifically, what role can the security industry play in what is seen as a growth area? Earlier this year, IFSEC International in London saw the launch of a new home automation zone featuring a replica smart home, showcasing a range of interconnected devices such as intruder alarms, CCTV, biometric readers, door entry solutions and locks, as well as wireless control of bli...
Insider threat is primarily focused on malicious threats to the company either by, or to, information technology assets For the past several years, information technology security concerns and priority regarding insider threats have steadily risen as evidenced by a variety of surveys across the IT security industry. Companies are becoming increasingly worried about insider threats. From the cyber security perspective, insider threat is primarily focused on malicious threats...










![[Download] The State Of Physical Access Control: Impact On The Enterprise](https://www.securityinformed.com/img/news/612/hid-access-2017-920.jpg)




![[Download] The Evolution Of Cards And Credentials In Physical Access](https://www.securityinformed.com/img/news/612/HID-whitepaper-Evolution of Cards and Credentials-920.jpg)






















