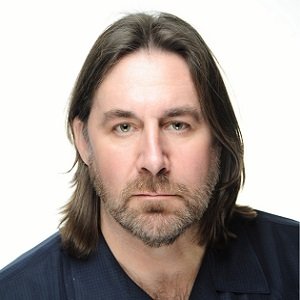
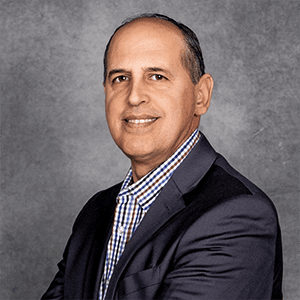
George Council

George Council
Vice President, Allied UniversalNews mentions
Buying security services can be a tricky business, and success requires a strategic approach involving multiple stakeholders and careful evaluation of proposals, including a scoring system that target...