Retail security applications - Expert commentary
When people think of control rooms, images from James Bond movies or intense action stories come to mind. What they fail to realise is the incredible level of ergonomics, technology, precision and craftsmanship required to create a top-notch command and control room. “These are rooms of complex functionalities, where hundreds of elements must be integrated and function in sync,” says Jim Coleman, National Sales Manager, AFC Industries. Professional teams from several different indus...
On 19th December, 2016, the news exploded with information about a vehicle attack on a Christmas market in Berlin that killed at least 12 people and injured more than 50 others. Less than a month before, the US State Department had warned about such attacks in public places throughout Europe, saying that extremist groups including the Islamic State and Al Qaeda were planning to focus on such locales during the Holiday Season. Two Types Of Vehicle Access Point To stop these attacks, security pr...
Real-time location systems allow organizations to communicate with visitors, employees, and staff in the event of an emergency Today's threat landscape is bigger and more broad than ever before, with an increasing number of emerging risks falling on the shoulders of security professionals in a variety of markets. Many of these leaders face the growing concerns of finding efficient, integrated solutions that provide protection from threats, but also can be used in everyday comm...
Access Control as a Service (ACaaS) has grown into a mainstream product offering from many access control manufacturers and the product offering is gaining significant growth in the market. With the adoption of this technology, end users and integrators need to ask several pertinent questions. This White Paper explores several important factors which must be understood in order for end users and integrators to make a sound decision when selecting an Access Control as a Service provider.What's...
Part 4 in our Intercoms in Security Series The ONVIF standard makes it simple to integrate the intercom with other ONVIF-compliant video management systems, access control solutions, and cameras Open standards are enabling new capabilities in the intercom market, some of it driven by the transition to systems based on Internet protocol (IP). Today’s most-used phrase in the intercom business is interoperability, given that the intercom is integrated with solutions s...
Part 3 of our Intercoms in Security Series: Zenitel’s Call Access Panel manages intelligible critical communications through a security operations center or control room Greater connectivity, security software enhancements, more customization, and better sound quality are some of the enhancements driving the intercom market.An advantage now offered on Code Blue’s emergency speakerphones include self-diagnosing software that monitors the status of the phones an...
Gaps in video from dropped video frames are a common problem. A web search on the phrase “dropped video frames” turns up links oriented towards gamers, YouTube videographers and even the world of video surveillance, discussing why frame drops happen and providing advice for coping with them. On Windows computers, video frame drops are a fact of life. Much of the advice can help reduce the number of frame drops, though never completely eliminate them. If you are an amateur filmmaker,...
One leading company has developed an identity management system using patents that verify the identity of an applicant Most enterprises rely on background screening providers to report accurate and complete information without understanding the litigious landscape. Security executives often have little input in how background checks are performed or by what provider, as this has become the domain of human resources (HR). A growing trend finds employers and their background scr...
By drawing data from a number of different sources and subsystems, including building automation, it is possible to move towards a truly smart environment Security solutions should be about integration not isolation. Many organizations are considering their existing processes and systems and looking at how to leverage further value. Security is part of that focus and is a central component in the move towards a more integrated approach, which results in significant benefits. G...
Part 1 in our Intercoms in Security Series Lambert-St. Louis International Airport uses Code Blue intercoms Organizations are demanding a new level of interoperability among mission-critical security systems. Intelligible audio, the ability to hear, be heard and be understood, is critical to communication, which is essential to the core security processes within an organization, as well as to emergency situations. Intelligible audio provides a platform to optimize v...
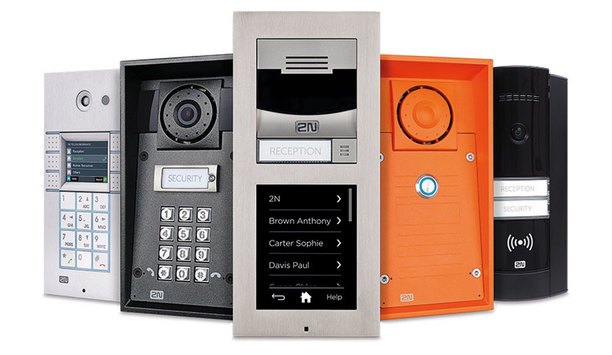
Part 2 of our Intercoms in Security Series The 2N Helios IP family intercoms present a comprehensive portfolio of security offerings for businesses and individuals Some integrators and end users may think of intercoms as older technology that isn’t required as part of a robust security system. Not true. Intercoms include innovative technologies that have developed rapidly, keeping pace with other categories. Just as cameras and access control systems have made techn...
Customers want and expect quality service, whether it is searching for an answer online or speaking to a live person via telephone or face-to-face How do you provide unparalleled, personalized customer service and support in a high-tech, self-service world? This blue ribbon is achievable by fusing the human component of superb customer care with user-friendly, cutting-edge solutions that are available around the clock. Technology has made it possible for customers to get assi...
Demand is increasing rapidly for more video, higher quality video, and increasing use of video for innovations like video analytics that provide enhanced security and operational intelligence. The growing demand is driving higher resolutions, larger camera counts, and longer retention times, which have all contributed to the growing importance and higher profile of data management and storage systems in the video surveillance industry. Customers need...
Over the years, video analytics has gained an unfavourable reputation for over-promising and under-delivering in terms of performance. One of the biggest complaints regarding video analytics has been its inability to correctly identify objects in situations which appear trivial to the human observer. In many cases, this has resulted in a tendency to generate substantial numbers of false alarms, while not detecting actual events accurately. This, together with a propensity for complex set-up proc...
The global market for card-based electronic access control (EAC) is projected to reach $10.1 billion by 2020 according to Global Industry Analysts. However, as credential technologies have evolved over the years, so have the ways users interact with them. Mobile Credentials One of the bigger developments over the past few years has been the increased adoption of mobile credentials, which allows users to access facilities via their mobile device....
CCTV security deployments require high reliability and availability in order to prove truly effective In recent years, there has been incredible growth in the security video surveillance market with law enforcement agencies embracing video surveillance to enhance security in problematic areas across cities. But these projects require connectivity to carry video feeds from multiple deployed CCTV cameras distributed over one or more sites, to the control room for viewing and rec...
It is critical to be able to clearly outline the end user’s potential return on investment Smart buildings are on the rise around the world, not only because a growing number of companies are considering their environmental impact, but also because of the dramatic cost savings that can be realized through integration. In every building that has an integrated security and access control system, an opportunity awaits to also integrate the building’s energy use, water...
Organizations are moving to align their physical and digital security initiatives, especially in today’s more connected world Organizations must address growing security threats using fewer resources in an increasingly challenging regulatory environment. They are looking to ensure data security while also protecting their facilities’ physical security. At the same time, their users are demanding more choices of smart cards, smartphones, wearables, and other mobile...
The top influencing trends in the security industry at ISC West 2017 will be big data, cyber security and the Internet of Things More than a thousand companies will be showing off their latest and greatest technologies and services at this year’s ISC West in Las Vegas. With so much to look at and experience, will you be able to pinpoint the next big thing or things that will dominate the security market in 2017? A good way to predict those upcoming trends is to look at w...
Smartphones offer a new alternative to traditional physical access control form factors such as smart cards or fobs. Convenience is the most obvious benefit, but there are others. Here are some advantages of using smart devices for access control: 1. Less vulnerability to cloning when compared to magstripe or low-frequency proximity cards. Digital credentials and mobile IDs are securely stored and protected. 2. Longer-distance communication, which allows readers to be mount...
Through new technology, applications and analytics, video surveillance systems are helping to make hospitals a safer place Healthcare organizations face many challenges. Federal mandates associated with the Affordable Care Act (ACA), changing reimbursement models, an ageing population and competition are among the most concerning issues. Unfortunately, so are safety and security. However, video surveillance is helping. Through new technology, applications and analytics, v...
Video analytics will be one of the first major domains within the security industry that will be radically transformed by AI When most people think of the term artificial intelligence, science fiction films both old and new tend to come to mind. Whether it’s the military network Skynet becoming self-aware in The Terminator and wiping out the majority of mankind with nuclear weapons, or the hosts in Westworld developing consciousness and turning against their human master...
The new scanner can quickly screen large groups of people without needing them to stop or slow down Most body scanners are designed to work one person at a time, checkpoint style. QinetiQ has developed a scanner that can be used in crowded places without having to slow down or stop moving targets. The body scanner, capable of detecting hidden explosives or weapons on a person, has been demonstrated publicly in the United Kingdom for the first time. The QinetiQ SPO-NX SPO-NX...
Successful critical thinkers are judged by results that almost always involve deliberation and intuition, logic and creativity Security and safety practitioners responding to evolving threats make decisions every day based on uncertainty, insufficient information, and too few resources for textbook solutions. Unsurprisingly, Chief Security Officers report that critical thinking, decision making, and communications skills are key characteristics for job success. But do we reall...
Real-time search analytics addresses one of the most important control room tasks - locating a person of interest If you have been to any of the many security industry tradeshows this year you will undoubtedly have seen and heard the phrase ‘next generation video analytics’. Is it just a catchy marketing phrase or is there more substance behind it? Video analytics as a technology has been with us for many years, but there has always been an air of confusion and mys...
Utility security staff have a responsibility to ensure they can identify risks associated with security threats Protecting North America’s power grid is a thankless job. Day in and day out, the good citizens of the United States and Canada wake up with the assumption that when they get out of bed each morning and flip on the lights, the room will illuminate, the coffee pot will come to life and their mobile phone will have been fully charged. After all, we live in a mode...
Cultural and hospitality venues are attractive targets for terrorists due to their public accessibility Over the past 40 years there have been numerous attacks carried out against cultural and hospitality venues in the furtherance of religious, ideological, criminal or political beliefs. By default, cultural and hospitality venues are attractive targets for terrorists due to their public accessibility, the volumes of visitors and guests or because of what the venue represents;...
Cloud-based solutions with mobile credentials and capabilities are simplifying multi-site management Facility managers and security operations staff are often bombarded with calls from multiple tenants, across several sites — each with unique needs — but traditionally they had no insight or control on the spot. Now, cloud-based solutions with mobile credentials and capabilities are simplifying multi-site management — enablin...
The Mexican border wall will be made of concrete; a substance that the president has used to some effect in his previous career The border with Mexico is an obvious starting point for the security community. Many had assumed that 'wall' would mean a high-tech fence or possibly just a virtual barrier of perimeter intrusion detection systems (PIDS), video surveillance with analytics and thermal imaging. However, during a press conference shortly before inauguration, Mr Trump put...
Counterterrorism tells antiterrorism about threats and antiterrorism tells counterterrorism about unusual or suspicious activities The most terrifying thing about terrorism is its reliance on the element of surprise. Most people don’t see the attacks coming, or don’t recognize the indicators when they see them. When terrorists strike, law enforcement is disadvantaged, the victims shocked and by the time an effective response is mounted the perpetrators are ofte...











![[Download] Choosing The Right Solution For Video Data Needs](https://www.securityinformed.com/img/news/612/hitachi-vms-editorial920.jpg)

![[Download] The State Of Physical Access Control: Impact On The Enterprise](https://www.securityinformed.com/img/news/612/hid-access-2017-920.jpg)