Cloud security - News
Dahua Technology, manufacturer of video surveillance products, has announced a strategic partnership with Pepper, an IoT platform-as-a-service, to allow the integration of its intelligent solutions into Dahua hardware. Highly secure cloud hosting Pepper’s U.S.-based platform powers connected devices around the world, delivering highly secure and private connected services via enterprise partnerships. Pepper’s platform-as-a-service approach caters to global consumer electronics manu...
OutSystems, provider of low-code application development platform, announced that it is the first low-code vendor to achieve two new cloud security certifications – ISO 27017 and ISO 27018. As organizations develop, run and share a higher percentage of their applications on the cloud, stakeholders across the business are trusting platform providers to ensure their cloud-based environments are secure. These certifications demonstrate the high level of commitment OutSystems has to ensuring...
Ping Identity, a provider of Identity Defined Security, announced that Kevin Sellers has joined the company's leadership team as the global chief marketing officer. Sellers leads all aspects of the company's marketing function, with a focus on accelerating expansion in the enterprise market and growing Ping's brand globally. An accomplished business leader with a strong track record of scaling global brands, Sellers brings more than 20 years of global marketing leadership experience in the te...
Userful Corporation, a globally renowned provider of AV-over-IP solutions for enhanced video communications, has been added by Inc. magazine, a renowned US-based business media entity, to its 38th annual Inc. 5000 list, one of the most prestigious rankings of the nation's fastest-growing private companies. The list offers unique insights into the most successful companies within the North American economy’s most dynamic segment, its independent small- and mid-sized businesses. Enterprise...
Microsoft and CyberArk are globally renowned companies in the identity management space for the security software sector, according to the latest Thematic scorecard from GlobalData. Identity management Identity management refers to software whose function is to ensure that the right people (or machines) have access to the parts of the IT system they require to fulfill their role. Both companies gained the highest Thematic score (5 out of 5) for the identity management theme in GlobalData&rsquo...
DMP is pleased to announce the expansion of its East Coast sales leadership team with the promotion of Ken Nelson to Director of Sales — East. Nelson joined DMP in 2017 as the Dealer Development Manager (DDM) for the company’s New York territory. In that short time, he has quickly proven his outstanding leadership abilities, making this transition a natural one. “Ken is a transformational sales leader,” says Jim Hawthorne, DMP Executive Director of Sales. “As one w...
The Spanish SMBs subscribed to Conexión Segura Empresas have avoided more than 80,000 potential cybersecurity incidents since the solution was launched in May. Of those, more than 89% of blocks occurred when users tried to access risky domains or websites, as a result of ‘phishing’. Combating rising cybercrime “The service that Telefónica Empresas offers to its customers has been launched at a moment of high level of cybercrime, in which a new threat is created...
Genetec Inc., globally renowned technology provider of unified security, public safety, operations, and business intelligence solutions, has announced that it is now offering multiple FICAM-(Federal Identity, Credential, and Access Management) certified options for its Security Center Synergis access control system. Personal Identity Verification In a market that has been traditionally weighed down by limited solutions that are often proprietary, these new options offer non-proprietary, open-a...
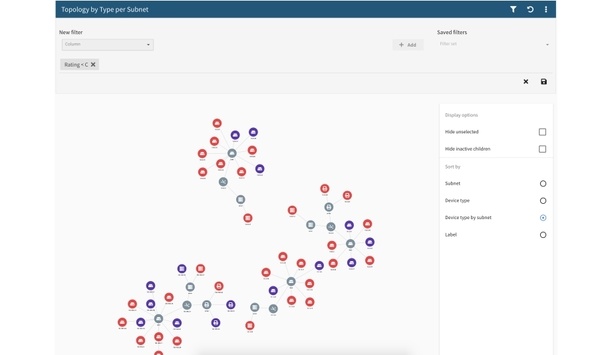
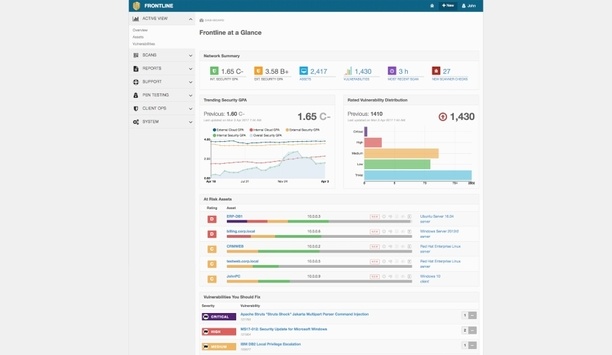
Digital Defense, Inc. announces Frontline Network Map, an innovative feature offering IT security and operations professionals enhanced visibility of vulnerabilities and threats found on small, medium, and large networks. Frontline Network Map is accessible within Frontline.Cloud, the company’s SaaS security assessment platform and is being demonstrated at Black Hat 2019 conference currently underway in Las Vegas, Nevada. Risk network segments Through the Network Map capability, Fronlin...
Keysight, the test and measurement vendor introduces its new Automotive Cybersecurity Program that delivers a broad cybersecurity portfolio, including hardware, software and services, to address the growing concern of cyber-attacks on connected vehicles. The cyber world is increasingly impacting the safe operation of automobiles, opening the risks of exposure, including malicious hacker activities. The new reality is that cyber-attacks against automobiles could result in the loss of human life....
Ping Identity, globally renowned provider of identity defined security solutions, has announced the release of PingCloud Private Tenant, a private cloud identity solution for the enterprise. Cloud identity, access management PingCloud Private Tenant provides cloud identity and access management (IAM) by combining highly-configurable capabilities within a dedicated environment. Enterprises can provide authentication for all users with a highly-configurable global authentication authority that...
Digital Defense, Inc. and The University of Texas at San Antonio (UTSA) Department of Computer Science jointly announced a partnership that will provide students and faculty with access to an award-winning cloud-based information security platform to further enrich the students’ cybersecurity education. UTSA students and faculty will be able to utilize Digital Defense’s flagship Frontline.Cloud platform to evaluate the security posture of applications, systems and networks in classr...
Johnson Controls announces Tyco Cloud, a new cloud-based security suite developed to help customers move costly and complex security infrastructure for access control and video surveillance to the cloud. With Tyco Cloud, organizations can reduce costs, improve enterprise security management and scale security operations on demand, providing unlimited possibilities to deliver security services over the internet. Accelerating digital transformation Tyco Cloud empowers this digital transformatio...
ExtraHop, globally renowned cloud-first detection and response solutions provider for hybrid enterprises, has issued a security advisory exposing several cases of third-party vendors ‘phoning home’ proprietary data without the knowledge of or authorization from their customers. The advisory serves as a warning to all enterprises to hold their vendors more accountable for how they use customer data. Phoning home proprietary data The newly-issued advisory defines phoning home as a ho...
Royal Boon Edam International is proud to announce that the Circlelock security locker is celebrating its 35th anniversary in 2019. Since entering the market in 1984, demand for this custom entry solution has continued to grow steadily in several important segments, including data centers, government and military, and commercial facilities. Principle of multi-factor authentication The Circlelock security booth owes its longevity to the principle of multi-factor authentication, whic...
Pulse Secure, global provider of software-defined Secure Access solutions to both enterprises and service providers, has announced that it has become a member of the MSPAlliance, the oldest managed services group and the only accrediting and standards based body created specifically for the managed services provider industry. Secure Access services Recognizing the push towards utility computing and an expectation for workforce mobility, multi-cloud performance and Zero Trust defenses, organiza...
Carbon Black, globally renowned cloud-native endpoint protection solutions provider, has released a white paper that proposes an updated cybersecurity kill chain model to help defenders stay ahead of evolving cyberattacks. Cybersecurity kill chain model The paper titled, ‘Cognitions of a Cybercriminal: Introducing the Cognitive Attack Loop and the 3 Phases of Cybercriminal Behavior’, delves into the various ways cybercriminals have evolved in recent years and offers specific guidel...
ExtraHop, global provider of cloud-first network detection and response solutions, has announced the appointment of experienced technology and software industry veteran Bill Ruckelshaus as its Chief Financial Officer (CFO). Ruckelshaus joins the company as it accelerates with more than 10x growth in cybersecurity and rapid expansion of its cloud product portfolio. He will hold a position on the ExtraHop executive leadership team, reporting to ExtraHop CEO Arif Kareem. Cybersecurity expert Ruc...
Expansion of the Aqua-Pivotal collaboration delivers comprehensive security for application development and production environments on PCF. Aqua Security, global platform provider for securing container-based and cloud native applications, has announced the public release of Aqua Security’s runtime protection for Pivotal Cloud Foundry (PCF). Users of Pivotal’s platform can download and install the Aqua Security for PCF service from Pivotal Services Marketplace, and deploy an end-to-...
The International Society of Automation (ISA) has announced the first founding members of its new Global Cybersecurity Alliance (GCA) - Schneider Electric, Rockwell Automation, Honeywell, Johnson Controls, Claroty, and Nozomi Networks. Global Cybersecurity Alliance ISA created the Global Cybersecurity Alliance to advance cybersecurity readiness and awareness in manufacturing and critical infrastructure facilities and processes. The Alliance brings end-user companies, automation and control sys...
Pivot3, global provider of intelligent infrastructure solutions, has announced the Virtual Security Operations Center (Virtual SOC), designed to address the need for security teams to access client workstations running video surveillance and other related systems in multiple locations without using expensive, dedicated client workstation hardware. Virtual Security Operations Center With the Pivot3 Virtual SOC, security teams can now get fully functional security workstation capabilities With...
Check Point announces three new security gateway appliance models: 16000 Base, 16000 Plus and the record breaking 26000 Turbo are extensions of Check Point’s new 16000 and 26000 gateway range which were introduced in June, presenting a complete line of high-end appliances with up to 64 networking interfaces, 16x 100 GbE (Gigabit Ethernet) or 40 GbE. Powered by the Check Point Infinity architecture, the 16000 and 26000 Security Gateways incorporate Check Point’s ThreatCloud and award...
Skybox Security releases mid-year update to its 2019 Vulnerability and Threat Trends Report, analyzing what’s shaping the threat landscape so far this year. Report Highlights from 2019 H1 Vulnerabilities in cloud containers have increased by 46 percent compared to the same period in 2018 and by 240 percent compared to 2017 Less than one percent of newly published vulnerabilities were exploited in the wild, with nine percent having any functioning exploit developed at all 2019 has add...
Ontic Technologies, the globally renowned provider of protective intelligence security software, delivers technology to empower security teams, in order to protect assets, employees and customers. In the modern world, organizations and their employees, clients, customers, and their physical assets may come under some kind of threat or attack, at any time. Protection that leverages deep analytics Investments in physical and other security systems have already been made, to protect these critica...
Radiflow, global provider of industrial cybersecurity solutions for industrial automation networks, has announced that the company has been recognized as the Global Customer Value Leader in IT/OT Security for Smart Buildings by the leading analyst firm, Frost & Sullivan. Cybersecurity protection This award from Frost & Sullivan highlights the growing importance that Radiflow is playing in providing cybersecurity protection for smart building operations as dramatically increasing number...
Using AI to bring focus to security, Avigilon Corporation, a Motorola Solutions company, has announced that it will once again be showcasing some of its latest and most innovative products and technologies at GSX 2019. Avigilon will showcase the next generation of video analytics, artificial intelligence, access control and cloud solutions, as well as some of the integrations with Motorola Solutions. Cutting-edge video analytics and AI Avigilon will be demonstrating how these latest technologi...
BlackWire Designs, a distributor in the custom installation market, announced that the company is now offering ProDataKey's (PDK) pdk.io, the industry's first completely cloud-based wireless access control system. The plug-and-play solution is easy for dealers to install, highly scalable, and simple for end users to manage. With its easy-to-use interface, pdk.io allows users to effortlessly manage cloud access control and see the status of every facility door in a single glance, while streamlin...
Eagle Eye Networks, the provider of cloud video surveillance worldwide, announced a new partnership with Salto Systems, a global provider of access control systems. In the new and improved Salto KS application, the Eagle Eye Cloud VMS Surveillance product has been integrated via cloud to provide Salto KS customers a more cyber-secure video experience connected to access control events. Within the Salto KS mobile app, a user can confirm a person’s identity before remotely granting access t...
Aqua Security, global platform provider for securing container-based and cloud native applications, has announced a new Private Offer capability enabling software licensing and procurement directly through Microsoft Azure Marketplace, allowing customers to utilize existing purchasing methods in place for Azure services. Aqua now offers a choice of flexible software acquisition models that allow customers to purchase licenses on Azure the way that works best for them. Software purchased directly...
Salient Systems is pleased to announce the appointment of Mr. Keith R. Aubele, CPP, LPP as a Senior Advisor to the Leadership Team responsible for the company’s expansion in the security and loss prevention vertical. Mr. Aubele will provide comprehensive national sales support and will work with the leadership team as a consultant for product line improvement, sales methods, and voice of the customer acquisition to help guide strategic planning. Loss prevention expert At The Home Depot,...