Building security - Expert commentary
Software as a Service (SaaS) provides computer equipment, OS, and software customized to the user’s purposes as a service. Access control can work in the same way. If you work in the physical security industry, especially concerning access control, you have probably heard about the term ‘ACaaS’ recently. ACaaS is a combination of ‘access control’ and ‘SaaS’ (Software as a Service). From a semantic point of view, ACaaS means providing cloud-based access c...
This is an era of digital revolution and with it comes dozens of new security dangers. Every gadget, from our smartphones to our security cameras, need some kind of protection from external hacking. However, how can we assure the safety of our devices, workplaces, etc.? Biometric security is one such security method that has emerged, since it is both efficient and perceived foolproof. It offers an additional layer of security for businesses and personal security systems. Biometric security syste...
Access control for buildings is nothing new. Early forms of security access for business security systems were introduced in the 1960s, as business owners and managers looked for alternatives to keys, as a result of needing to frequently replace them, when there was a change in personnel. It’s only in recent years that the urgency to implement smarter, more efficient, and convenient forms of access control has increased, in the context of public and private sector digital transformation....
Fingerprint biometrics is hugely relevant in the current landscape. Even amidst other newer developments, fingerprint authentication provides convenience and affordability. There are talks rife about how the coronavirus pandemic has changed the outlook towards fingerprint biometrics. What is currently the most used authentication technology is being speculated to be unsafe, when compared to other touchless biometrics and that its usage in the future would decrease significantly. However, the adv...
As we enter into 2022, there is still a level of uncertainty in place. It’s unclear what the future holds, as companies around the world still contend with the COVID-19 pandemic. Remote working has been encouraged by most organizations and the move to a hybrid working system has become ‘business as usual’, for the majority of businesses. Some have reduced their office space or done away with their locations altogether. Following best security practices With all this change in...
There is no denying that the COVID-19 pandemic has radically changed the way we work. In May 2021, 31% of the countries workforce was still working remotely, with 71% of businesses in professional, scientific, and technical industries remote-working. Work patterns shifting Although the conversation often focuses on office workers, the COVID-19 pandemic has impacted the way many other, non-office sectors operate. In the security industry, since the introduction of lockdowns and social distancin...
They say nothing stays the same for long, and this has never been truer than in today’s world of technology and innovation. The 21st century has seen rapid changes and every day brings a new update in one of the many segments of technology. Technology is evolving at such a rapid rate, due to a phenomenon dubbed accelerating change. Each new improvement is now a stepping stone, enabling stronger and better generations of technology, at faster speeds. Accelerating change evolving across all...
Businesses large and small rely on their CCTV systems to deter intruders and provide recorded evidence of security incidents. Overtime, CCTV has evolved to offer real-time intrusion detection and monitoring, and businesses now expect easy, secure and anytime access to cameras, and data. For that, they need connected CCTV systems. These modern installations can benefit from cellular connectivity, helping businesses protect their sites, while also supporting enhanced capabilities for CCTV to deliv...
In the field of access control, face recognition has come a long way. Once considered too slow to authenticate people's identities and credentials in high traffic conditions, face recognition technology has evolved to become one of the quickest, most effective access control identity authentication solutions across all industries. Advancements in artificial intelligence and advanced neural network (ANN) technology from industry leaders like Intel have improved the accuracy and efficiency of fa...
Gregor Schlechtriem has worked in the access control market for over 20 years and is now responsible for the Access & Intrusion Business Unit at Bosch Building Technologies. In this interview, the expert talks about key industry trends, the impact of the COVID-19 (Coronavirus) pandemic, technical innovations and his company’s strategy. Mr. Schlechtriem, you have many years of experience in the security technology market. What is your background and what are your responsibilities as Se...
Recent cyber-attacks have disabled and even shut down physical assets. Robust foundational security and training staff, able to recognize an attack can help mitigate the threat, as ABB’s Rob Putman explains. Edge devices and data analytics As cyber security specialists, we must navigate an ever-changing threat landscape, one that is made even more complex by the increased interconnectivity between Operational Technology (OT) and Information Technology (IT), as companies look to leverage...
The COVID-19 pandemic is only accelerating the expansion of Automation, Robotics, Machine Learning (ML) and Artificial Intelligence (AI), and changing how people live their daily lives. This expansion leads the way with technologies that are developed to solve problems, improve operations, streamline processes and assist people, to focus on learning new skills, creativity, and imagination. Transformation of the physical security industry One of the latest industries to be permanently transform...
Schools were never designed and built with social distancing in mind. So it’s perhaps not surprising that as children returned to schools for the autumn term this year, the prospect of outdoor classes and assemblies was mooted in the media and by the Government. Many in the education sector are making the case that, should there be further COVID-19 outbreaks, in the coming months, it would be better to utilize outside space, rather than resort to closing schools. In the COVID-19 era, head...
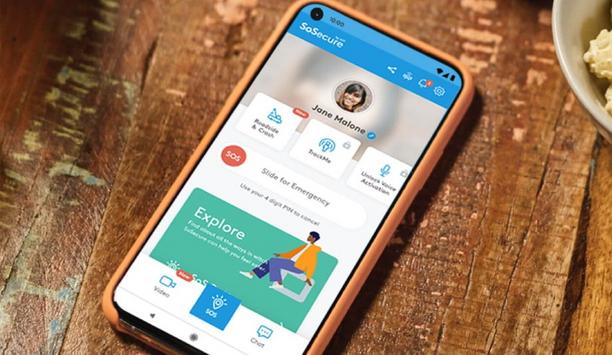
The past year has elevated consumer awareness about personal safety, from COVID-19 issues to social unrest, making safety top-of-mind and the need for personal safety solutions, even more prevalent. In addition, consumers spent more time at home, as schools closed, events were canceled and remote work increased. This prompted two major shifts that, in my opinion, most significantly opened the need for and raised the popularity of mobile safety solutions. Demand for grocery and food delivery...
Today’s organizations face numerous diverse threats to their people, places and property, sometimes simultaneously. Security leaders now know all too well how a pandemic can cripple a company’s ability to produce goods and services, or force production facilities to shut down, disrupting business continuity. For example, a category three hurricane barreling towards the Gulf of Mexico could disable the supplier’s facilities, disrupt the supply chain and put unexpected pressure o...
Intrusion alarm systems are currently facing a growing number of potential error sources in the environment. At the same time, alarm systems must comply with increasingly demanding legal requirements for sensors and motion detectors. As a future-proof solution, detectors equipped with Sensor Data Fusion technology raise the level of security while reducing the risk of cost- and time-intensive false alarms. This article provides a comprehensive overview of Sensor Data Fusion technology. Anti-mas...
From analog to digital, from stand-alone to interlinked, building systems are in a state of transition. Moreover, the rate of change shows no sign of slowing, which can make it difficult to keep up to date with all the latest developments. If asked to pinpoint the single biggest driver of this revolution, one could point out the growing clamor for platform convergence. A security guard in a building doesn’t want to use different systems to check video cameras, fire alarms or if someone ha...
Today, we live in a technology-obsessed age. Whichever way you look, it’s hard to avoid the increasing number applications, products and solutions that continue to redefine the boundaries of what we previously thought possible. From autonomous vehicles and edge computing to 5G and the Internet of Things, all facets of our lives are continuing to evolve, thanks to an endless stream of differentiated innovations. In this article, we’ll be focusing on the latter of these - the Internet...
The ‘new normal’ was all we heard about when it came to the working model shift after the pandemic hit. Businesses worldwide adopted working from home, and then the hybrid model: a balance of remote work and office work. And according to a recent survey by 451 Research, nearly 80% of organizations surveyed said they have implemented or expanded universal work-from-home policies as a result of COVID-19, whilst 67% expect these policies to remain in place either permanently or for th...
Most consumers are enjoying the convenience brought by electronic locks. With the existence of electronic locks, people no longer need to be restricted by keys. There are a variety of unlocking methods and more convenient remote control unlocking options. Suppose, you are going on vacation, and with the presence of an electronic lock, you can easily enter your house with your babysitter, without a spare key. Of course, not only smart homes, but also some infrastructure and commercial buildings...
Household adoption of smart home systems currently sits at 12.1% and is set to grow to 21.4% by 2025, expanding the market from US$ 78.3 billion to US$ 135 billion, in the same period. Although closely linked to the growth of connectivity technologies, including 5G, tech-savvy consumers are also recognizing the benefits of next-generation security systems, to protect and secure their domestic lives. Biometric technologies are already commonplace in our smartphones, PCs and payment cards, enhan...
In the past decade, we’ve seen an unfortunate increase in gun-related incidents on school campuses, making security and policy efforts a top priority for educational facilities nationwide. While the causes for this increase are hotly debated in and around the education community, the facts remain that specific steps can be taken to mitigate risks. To tackle this issue, officials from campus stakeholders, law enforcement officials, architects, and security personnel, have met to find solut...
The impact of the COVID-19 pandemic has accentuated our digital dependency, on a global scale. Data centers have become even more critical to modern society. The processing and storage of information underpin the economy, characterized by a consistent increase in the volume of data and applications, and reliance upon the internet and IT services. Data centers classed as CNI As such, they are now classed as Critical National Infrastructure (CNI) and sit under the protection of the National Cybe...
Cloud-based technology can reduce IT costs, streamline application management and make infrastructure more flexible and scalable. So, it’s no surprise that cloud video surveillance solutions (also known as video surveillance as a service or VSaaS) are gaining momentum in a big way. In fact, according to recent reports, the VSaaS market is forecasted to increase at a compound annual growth rate of 10.4% by 2025. But some company owners may wonder – what services does a cloud model de...
Everyone in security understands the significance of events, such as trade shows, road shows, seminars, galas and meet-and-greets. Whether virtual or in-person, these gatherings are important for a number of reasons. Role of security events For start-ups and high-profile manufacturers alike, security events have been the place to display new products, interact with key customers and strengthen existing partnerships. They serve as a forecast for evolution, showcasing the latest advancements in...
For many businesses and organizations, the term 'authentication' is synonymous with 'password' or 'multi-factor authentication (MFA)’. However, because today's business ecosystem is complex and stretches across distributed workforces with work from home, BYOD policies, and multiple cloud environments, it is very challenging to efficiently recognize and authenticate identities of people, processes, and devices throughout the enterprise using traditional methods. The problem with passwords...
The evolution of smart video technology continues at pace. As in many other industries, the onset of the COVID-19 pandemic expedited timelines and the artificial intelligence (AI) video world is continuing its rapid evolution in 2021. As video demand and the use of AI to make sense of the visual data increase, the number of cameras and subsequent data produced are growing rapidly, and these are forcing the creation of new edge architectures. Cameras and AI in traffic management ‘Smart f...
TOA Corporation (UK) Ltd discuss what changes COVID-19 has bought to the installation of VA/PA Systems and how the integration of IP has impacted on that. With a year and a half of global uncertainty, we have seen huge changes in what VA/PA systems will need to deliver in order to provide safe and robust solutions with advanced zone and directional messaging. The impact of COVID has pushed installers to re-think what end-users need long-term to manage any future changes in guidelines especiall...
Small and medium businesses of all kinds encountered unprecedented challenges during the COVID-19 pandemic. And now that businesses have reopened, they are facing new obstacles through each stage of recovery. Business owners need to look for solutions that can help them manage these issues now and beyond. Challenges ranging from lack of cash flow to staffing challenges to IT security issues for businesses with remote workers can be lessened by security and automation solutions. One of the main...
It has long been recognized that no one is safe from cyber-attacks, but some sectors face a much higher level of threat than others. Critical infrastructure sectors such as utilities, energy and industrial manufacturing are some of those that face an intense level of interest from cyber criminals and nation-state groups across the globe. The impacts of a successful attack can have detrimental consequences, for both the cyber and physical side of the business, in terms of business disruption, ec...