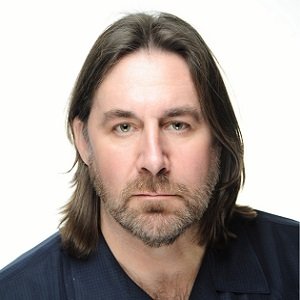
Markus Lahtinen

Markus Lahtinen
Researcher and Lecturer at Lund University, LUSAX Security InformaticsMarkus Lahtinen has since 2006 been researching topics concerning the long-term changes of the physical security industry as well as the evolving role of the corporate security director. More generally the LUSAX program has focused on the industrial and end-user consequences of increased digitization. LUSAX is driven by the academic ambition that close and Frequent contact with industry stakeholders is necessary for producing current and relevant research
Interaction design, research, behavioral aspects related to IT development/use
Articles by Markus Lahtinen
Since 2006, the LUSAX research program at Lund University in Sweden has investigated the effects of digitization on the physical security industry. This article will look into the...
Law enforcement and pure problem-solving skills will play less of a role for the future security director Much effort has been put down in the professionalization of security work....