Cyber security - News
Arecont Vision Costar, globally renowned network-based video surveillance solutions provider, has announced that Intelligent Network Sales, LLC has joined the Authorized Manufacturer’s Representative Program. The experienced firm will deliver pre-sales support to AV Costar customers and partners across the New England Region of the United States. Intelligent Buildings expert “Steve Chase and his team bring years of experience in supporting customers throughout the New England regio...
A study from Exabeam, the Smarter SIEM™ company, revealed that more than one-third of security professionals' defensive blue teams fail to catch offensive red teams. The survey, conducted at Black Hat USA 2019, also showed that 68% find red team exercises more effective than blue team testing, and more companies are practising red over blue team testing. As cyberattacks become increasingly sophisticated and hack techniques become more highly targeted, organizations must learn how di...
Dahua Technology, manufacturer of video surveillance products, has announced a strategic partnership with Pepper, an IoT platform-as-a-service, to allow the integration of its intelligent solutions into Dahua hardware. Highly secure cloud hosting Pepper’s U.S.-based platform powers connected devices around the world, delivering highly secure and private connected services via enterprise partnerships. Pepper’s platform-as-a-service approach caters to global consumer electronics manu...
Qualitest, the independent software testing and quality assurance company, opens its new headquarters in Central London following a period of worldwide growth. Serving as a central location with easy access to Qualitest’s US, Israel, India and Romanian offices, London is also a base for prominent existing clients as well as a wide array of companies seen as prospective clients. The new office, based close to Liverpool Street station, brings together employees located across greater London...
Global cybersecurity firm GRA Quantum announces the launch of its comprehensive offering, scalable security suite, providing solutions based on a combination of managed security services and professional services, tailored to the specific needs of each client. Scalable security suite was created to give small to mid-sized organizations a running start when it comes to security, providing the same standard of security controls as large enterprises. Providing security solution According to GRA...
Userful Corporation, a globally renowned provider of AV-over-IP solutions for enhanced video communications, has been added by Inc. magazine, a renowned US-based business media entity, to its 38th annual Inc. 5000 list, one of the most prestigious rankings of the nation's fastest-growing private companies. The list offers unique insights into the most successful companies within the North American economy’s most dynamic segment, its independent small- and mid-sized businesses. Enterprise...
Microsoft and CyberArk are globally renowned companies in the identity management space for the security software sector, according to the latest Thematic scorecard from GlobalData. Identity management Identity management refers to software whose function is to ensure that the right people (or machines) have access to the parts of the IT system they require to fulfill their role. Both companies gained the highest Thematic score (5 out of 5) for the identity management theme in GlobalData&rsquo...
BitSight, the Standard in Security Ratings, announced BitSight Enterprise Analytics, the latest Security Performance Management solution available on the BitSight platform. BitSight Enterprise Analytics helps security and risk leaders quickly gain insight into the impact of risk introduced at the organizational group level – from subsidiaries to business units and departments – enabling them to identify the areas of highest risk concentration within their organizations. The solution...
DMP is pleased to announce the expansion of its East Coast sales leadership team with the promotion of Ken Nelson to Director of Sales — East. Nelson joined DMP in 2017 as the Dealer Development Manager (DDM) for the company’s New York territory. In that short time, he has quickly proven his outstanding leadership abilities, making this transition a natural one. “Ken is a transformational sales leader,” says Jim Hawthorne, DMP Executive Director of Sales. “As one w...
The Spanish SMBs subscribed to Conexión Segura Empresas have avoided more than 80,000 potential cybersecurity incidents since the solution was launched in May. Of those, more than 89% of blocks occurred when users tried to access risky domains or websites, as a result of ‘phishing’. Combating rising cybercrime “The service that Telefónica Empresas offers to its customers has been launched at a moment of high level of cybercrime, in which a new threat is created...
Genetec Inc., globally renowned technology provider of unified security, public safety, operations, and business intelligence solutions, has announced that it is now offering multiple FICAM-(Federal Identity, Credential, and Access Management) certified options for its Security Center Synergis access control system. Personal Identity Verification In a market that has been traditionally weighed down by limited solutions that are often proprietary, these new options offer non-proprietary, open-a...
IronYun, an AI-based video surveillance software company and Razberi Technologies, an open-platform video surveillance hardware company entered into a technology partnership, marking a turning point for IronYun’s physical security video surveillance solutions. With the introduction of IP cameras, physical security has become a strain on network bandwidth. Security response times can mean the difference between life or death. The technology required to store and quickly retrieve 4 mega pix...
Global provider of critical comfort and security solutions primarily in the residential sector, Resideo Technologies, Inc. has announced that Bob Appleby will join its ADI Global Distribution business as vice president and general manager of ADI North America, effective immediately. ADI North America head In his new role, Appleby will oversee all of ADI North America’s business operations across the United States, Canada and Puerto Rico, and will help ADI deliver on financial commitments...
Johnson Controls has updated its popular Illustra Pro camera family with a new generation of Illustra Pro Mini-Domes featuring Smart Wide Dynamic Range. Offering a choice of 2, 3, 5 and 8 megapixel models and a variety of lens options, the new Pro Mini-Domes are ideal for a wide range of deployments in both medium and large-sized facilities. Smart WDR technology This new Smart Wide Dynamic Range (WDR) technology built into the new Mini-Domes greatly improves the quality of images captured in v...
Keysight, the test and measurement vendor introduces its new Automotive Cybersecurity Program that delivers a broad cybersecurity portfolio, including hardware, software and services, to address the growing concern of cyber-attacks on connected vehicles. The cyber world is increasingly impacting the safe operation of automobiles, opening the risks of exposure, including malicious hacker activities. The new reality is that cyber-attacks against automobiles could result in the loss of human life....
Ping Identity, globally renowned provider of identity defined security solutions, has announced the release of PingCloud Private Tenant, a private cloud identity solution for the enterprise. Cloud identity, access management PingCloud Private Tenant provides cloud identity and access management (IAM) by combining highly-configurable capabilities within a dedicated environment. Enterprises can provide authentication for all users with a highly-configurable global authentication authority that...
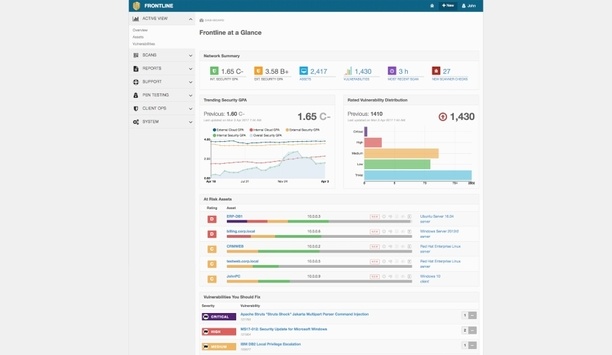
Digital Defense, Inc. and The University of Texas at San Antonio (UTSA) Department of Computer Science jointly announced a partnership that will provide students and faculty with access to an award-winning cloud-based information security platform to further enrich the students’ cybersecurity education. UTSA students and faculty will be able to utilize Digital Defense’s flagship Frontline.Cloud platform to evaluate the security posture of applications, systems and networks in classr...
ThreatQuotient™, a security operations platform innovator, announces new partnerships with global distributors Ectacom, Nihon Cornet and StarLink. Following international expansions into Central Europe and Australia in 2018, ThreatQuotient’s latest value added distributor (VAD) agreements leverage an extensive network of channel partners and solution providers to broaden the reach of their security operations platform across the Middle East, Asia-Pacific, Japan and China. Additional...
Johnson Controls announces Tyco Cloud, a new cloud-based security suite developed to help customers move costly and complex security infrastructure for access control and video surveillance to the cloud. With Tyco Cloud, organizations can reduce costs, improve enterprise security management and scale security operations on demand, providing unlimited possibilities to deliver security services over the internet. Accelerating digital transformation Tyco Cloud empowers this digital transformatio...
Everbridge, Inc., the global provider of critical event management (CEM) and enterprise safety software applications to help keep people safe and businesses running, announced the acquisition of NC4, a global provider of threat intelligence solutions that empower businesses, government organizations, and communities to assess and disseminate risk data and information to manage and mitigate the impact of critical events. The combination of NC4’s real-time threat intelligence and analyst te...
ExtraHop, globally renowned cloud-first detection and response solutions provider for hybrid enterprises, has issued a security advisory exposing several cases of third-party vendors ‘phoning home’ proprietary data without the knowledge of or authorization from their customers. The advisory serves as a warning to all enterprises to hold their vendors more accountable for how they use customer data. Phoning home proprietary data The newly-issued advisory defines phoning home as a ho...
Most enterprises today deploy a multitude of touchpoints where consumers can interact and access the information they require. For many organizations, APIs (Application Programming Interfaces) are the bread-and-butter for enabling inter-enterprise process automation, IoT devices and mobile applications. Even though they are working behind the scenes, APIs are ubiquitous. They help to deliver sports updates, post online messages, order food – enabling everything online. To stay competitive...
Pulse Secure, global provider of software-defined Secure Access solutions to both enterprises and service providers, has announced that it has become a member of the MSPAlliance, the oldest managed services group and the only accrediting and standards based body created specifically for the managed services provider industry. Secure Access services Recognizing the push towards utility computing and an expectation for workforce mobility, multi-cloud performance and Zero Trust defenses, organiza...
Carbon Black, globally renowned cloud-native endpoint protection solutions provider, has released a white paper that proposes an updated cybersecurity kill chain model to help defenders stay ahead of evolving cyberattacks. Cybersecurity kill chain model The paper titled, ‘Cognitions of a Cybercriminal: Introducing the Cognitive Attack Loop and the 3 Phases of Cybercriminal Behavior’, delves into the various ways cybercriminals have evolved in recent years and offers specific guidel...
ExtraHop, global provider of cloud-first network detection and response solutions, has announced the appointment of experienced technology and software industry veteran Bill Ruckelshaus as its Chief Financial Officer (CFO). Ruckelshaus joins the company as it accelerates with more than 10x growth in cybersecurity and rapid expansion of its cloud product portfolio. He will hold a position on the ExtraHop executive leadership team, reporting to ExtraHop CEO Arif Kareem. Cybersecurity expert Ruc...
Expansion of the Aqua-Pivotal collaboration delivers comprehensive security for application development and production environments on PCF. Aqua Security, global platform provider for securing container-based and cloud native applications, has announced the public release of Aqua Security’s runtime protection for Pivotal Cloud Foundry (PCF). Users of Pivotal’s platform can download and install the Aqua Security for PCF service from Pivotal Services Marketplace, and deploy an end-to-...
The International Society of Automation (ISA) has announced the first founding members of its new Global Cybersecurity Alliance (GCA) - Schneider Electric, Rockwell Automation, Honeywell, Johnson Controls, Claroty, and Nozomi Networks. Global Cybersecurity Alliance ISA created the Global Cybersecurity Alliance to advance cybersecurity readiness and awareness in manufacturing and critical infrastructure facilities and processes. The Alliance brings end-user companies, automation and control sys...
Pivot3, global provider of intelligent infrastructure solutions, has announced the Virtual Security Operations Center (Virtual SOC), designed to address the need for security teams to access client workstations running video surveillance and other related systems in multiple locations without using expensive, dedicated client workstation hardware. Virtual Security Operations Center With the Pivot3 Virtual SOC, security teams can now get fully functional security workstation capabilities With...
Check Point announces three new security gateway appliance models: 16000 Base, 16000 Plus and the record breaking 26000 Turbo are extensions of Check Point’s new 16000 and 26000 gateway range which were introduced in June, presenting a complete line of high-end appliances with up to 64 networking interfaces, 16x 100 GbE (Gigabit Ethernet) or 40 GbE. Powered by the Check Point Infinity architecture, the 16000 and 26000 Security Gateways incorporate Check Point’s ThreatCloud and award...
Skybox Security releases mid-year update to its 2019 Vulnerability and Threat Trends Report, analyzing what’s shaping the threat landscape so far this year. Report Highlights from 2019 H1 Vulnerabilities in cloud containers have increased by 46 percent compared to the same period in 2018 and by 240 percent compared to 2017 Less than one percent of newly published vulnerabilities were exploited in the wild, with nine percent having any functioning exploit developed at all 2019 has add...