Central Monitoring - Expert commentary
Physical security isn’t a one-time project or a static system. It’s a dynamic, ongoing process and program that requires constant attention and management to remain effective. While the initial implementation of a security system — what we often call Day 1 — is critical, the ongoing maintenance, service, and adjustments made after systems are operational, or Day 2, are equally essential. Security program long-term Organizations that fail to focus on post-occupancy sec...
As urban populations grow and security challenges evolve, major Californian cities like Los Angeles, San Francisco and San Diego have increasingly turned to advanced surveillance systems to enhance public safety. Surveillance infrastructure Between 2022 and 2024, these cities have made significant strides in upgrading their surveillance infrastructure, driven by concerns over crime, public safety, and the need for more sophisticated emergency response systems. This article explores how...
In the realm of physical security, the distinction between being perceived as a security vendor and a security partner holds great importance. While both may seem interchangeable at first glance, how an organization is viewed by its clients can have a huge impact on the success of its security programs. At the heart of this differentiation is the concept of relationships and how they shape the dynamics between providers and their clients. Time, care, and diligence For security vendors s...
Changing customer needs can make specifying an alarm system that will continue to deliver in the long term a challenge. However, the latest modular alarm solutions provide the opportunity to build a more individualized system from the outset, as well as offering the ability to up-scale in the future without causing disruption. Martin Wilson, North EMEA Regional Director at Resideo, looks at how alarm specialists can use this style of solution to both benefit customers and build their own busine...
Amidst the challenges of a prevailing economic downturn, the retail sector finds itself grappling with an unparalleled rise in incidents of shoplifting, theft, and burglaries. The disconcerting scenes witnessed on London’s Oxford Street in August 2023, where crowds gathered, looting as many stores as possible, sent shockwaves across the nation’s retailers. This alarming surge in retail crime has put retailers on high alert, as they contend with a rising tide of security concer...
The average business owner or investor has some kind of security precaution in place, especially in the after-hours when there are fewer deterrents to inhibit criminal activity. Security guards, video surveillance systems, motion sensor lights, or even just fake cameras placed around the property are some of the common options people choose. Future of overnight security Smart business owners are starting to realize, however, that some of these traditional security measures are becoming...
The autumn equinox, which marks the start of autumn, occurs this weekend on Saturday, September 23. With darker evenings ahead, the experts at ADT have shared five ways to maximize your home's security. Author's quote Michele Bennett, General Manager at ADT UK&I comments: “Opportunistic thieves use darkness to their advantage, so it’s no surprise that the number of burglaries committed increases when the darker nights draw in." He adds, "Our 2022 burglary report found that bu...
It’s no secret that the data security sector is constantly changing. It has an annual CGR of about 12.3%. Future trends in data security Much of this has to do with the rise of cybercrime in recent years, with reports showing that cyberattacks happen as often as every 39 seconds. To combat the growing rate of cybercrime, data security has been on the rise. As we journey further into this era, it becomes evident that a spectrum of significant trends is molding the future of data se...
GSX 2023 marks a poignant moment for the security industry as an increasingly complex risk landscape converges with the acceleration of technology innovation. Emerging from this environment are three key trends that will dominate the conference and the future of the security industry: (i) the adoption of AI, (ii) the use of predictive analytics, and (iii) a hybrid global and local risk management approach. As Chief Security Officer of Crisis24, a GardaWorld company, I regularly advise cli...
Daniel May of Consort reviews the integration of access control systems in healthcare settings, outlining the benefits and key considerations decision-makers must make throughout product specifications. From patient safety and traversal to the protection of sensitive data and pharmaceuticals, healthcare environments are faced with several operational challenges. And where security remains at the forefront of decision-making, modern access control systems may often hold the answers. Physi...
Global transportation networks are becoming increasingly interconnected, with digital systems playing a crucial role in ensuring the smooth operation of ports and supply chains. However, this reliance on technology can also create vulnerabilities, as demonstrated by the recent ransomware attack on Nagoya Port. As Japan's busiest shipping hub, the port's operations were brought to a standstill for two days, highlighting the potential for significant disruption to national economies and supply cha...
Physical security is essential for a modern production facility, users don’t want just anyone entering the building or accessing secure areas. But what about production machinery? Machine authentication is often a missing link in the security plan for manufacturers. Why machine authentication? Most manufacturers have made significant investments in physical access control (PAC) for production facilities. Few shops currently hand out physical keys to employees or leave the building...
Mass attacks continue to lead the news far too often. All are horrific and disturbing, but the heartbreaking tragedies that have unfolded on school campuses touch us the deepest and have the most profound effects on our communities. NTAC statistics According to a January 2023 report from the United States Secret Service National Threat Assessment Center (NTAC), K-12 events accounted for 6% of all mass attacks in public and semi-public spaces between 2016 and 2020. 6% may strike some as being...
Organizations of all types have made it a priority to better track who is coming and going inside their facilities and on their property. This can include an HVAC technician who needs to be inside a building for several hours to fix a faulty air conditioning unit or a parent who volunteers each week in their child’s school. Technology-based visitor management With considerable advancements in visitor management systems in recent years, organizations are now benefiting from technology-b...
Our recent survey on the state of access control in 2023 showed that HID partners and end users, as well as security and IT professionals, may have varying needs and concerns but nearly all agree on one thing: the need for sustainable solutions. Operational transparency In fact, sustainability was a top issue for almost 90% of our survey respondents. Our end users and their consumers are primarily driving this demand, with ever-increasing numbers asking for operational transparency...
There’s been a long history of people thinking of “gates, guards, and guns” when referring to physical security. And for a long time, this was the norm. When analog cameras required significant amounts of wiring and a dedicated guard to watch said feeds (think about any action movie from the 90s), the assumption was that security was protecting assets, but had little to do with the overall business. Defining security with recent advancements Fast forward to more recen...
What would it take to make an office building perfectly secure, with 100% impregnability? Would you put padlocks on every door and window, and security gates in every corridor? Certainly, this would be very secure, but it doesn’t take a security expert to see how such a setup would be a huge waste of resources, nor would it be convenient for the people who need to work in the building. Cybersecurity challenges But while most busine...
Regardless of their experience level or location, there is always a sense from close protection practitioners that there's a hunger to get back into the field and closer to the action. And why not? International travel coupled with diverse and challenging environments is all tied to a sense of mission. This is quintessential for close protection teams and starts with business travel. Travel concerns But, while increasing, it's safe to say that business travel is unlikely to return to...
DevSecOps is a vital strategy with automated security included in every phase of software development. Implementing DevSecOps means application and infrastructure security becomes a shared responsibility amongst the development, operations, and security teams which maximizes protection at every level of the organization. Investing in DevSecOps strategies According to a recent report conducted by the Neustar International Security Council (NISC), an elite group of cybersecurity professi...
As the cost-of-living crisis intensifies in 2023, owners of construction companies will place a greater emphasis on environmentally-friendly materials, public safety, and strategies to increase value. Physical protection Key events in 2023 will have an impact on the physical protection of people, property, and businesses. King Charles III's coronation in May will be the focus of nationwide large-scale gatherings and celebrations and is already receiving security preparations. Even though this...
The nuances of data privacy continue to bombard organizations from all angles, and, amid the impending sunset of Universal Analytics (UA), it’s time to stop playing catch-up. Instead, by enacting future-proofing strategies around data as a first port of call, long-term compliance can be achieved as an automatic byproduct. Data privacy At data privacy’s ‘sunrise’, companies’ efforts were largely targeted towards the customer, ensuring that the ever-growing extent o...
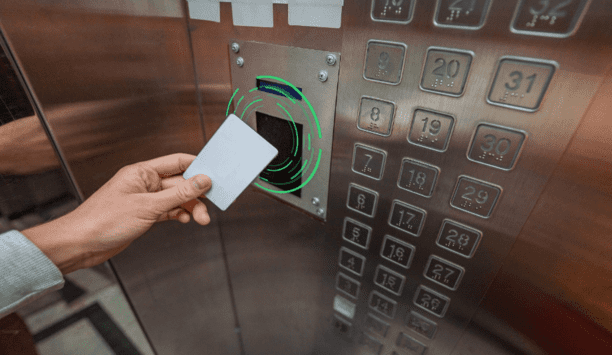
RFID and emerging mobile access technologies are easy to implement and allow elevator access to be integrated with other access control solutions throughout the building, from building entry to printer access. The right RFID reader can help reduce complexity by migrating diverse older technologies into a single convenient solution. Ways RFID Works Radio-frequency identification (RFID) and smartphone-based credentialling systems using Bluetooth® Low Energy (BLE) or Near-Field Communication...
You’re no psychic. You probably don’t have the power of clairvoyance. But guess what? When it comes to your security, none of that matters. You can still create future-proof security by properly equipping yourself. Here’s how. Understanding access control Security is changing faster than ever before. With new threats inside the workplace and smaller security teams taking on more tasks, IT and security personnel must automate their processes using new technology. One difficu...
Although inflated fuel prices have somewhat settled since the summer, recent changes in legislation mean construction sites are particularly vulnerable to attempted fuel thefts. Read on to find out what’s changed, and what’s proving effective in mitigating the threat. What are the changes? As of April, this year red diesel can no longer be used in a range of vehicles, including those in construction. That means fuel bowsers are now filled with the same white diesel available to m...
Nowadays the Internet of Things has become an integral part of business around the world. The enhanced functionality made possible by the Internet of Things (IoT) and associated technologies are responsible for many of the major changes seen across society today. Video surveillance Video surveillance is one area that experiences substantial evolution driven by IoT technology. The intelligent monitors and sensors of the IoT combined with emerging high-speed network solutions promise to improve...
It’s clear that despite recent layoffs in the tech industry and general unease about the economy, there are still significant gaps in the number of jobs available and the amount of workers available to fill them. According to the Labor Department, there are 5.5 million more job openings than workers available. The physical security industry is not immune to these shortages. Last fall, Allied Universal reported being unable to fill thousands of open roles nationally while other smaller se...
For the past few years, security professionals have had to change the way that they go about protecting their organizations. From challenging old assumptions around access control through to implementing more access management and authentication policies, security has been at the heart of how companies have responded to the pandemic. The journey to more modern security processes that could support more flexible working was a rapid one. Remote work programs have bedded in, based on how IT secur...
One of the biggest security trends in the last two years has been the adoption of cloud-based services, spearheaded mainly by an increasing number of video surveillance-as-a-service (VSaaS) offerings. VSaaS market value According to MarketsandMarkets Research, the global VSaaS market value is expected to reach $6.2 billion by 2026. This growth is propelled by demand for remote access video services, less local hardware to maintain, new internet-enabled devices, and a lower total cost of owners...
Cloud-based applications and platforms revolutionize supply chain management, helping stakeholders scale operations from small businesses to complex enterprises. Cloud supply chain solutions are showing significant increases in implementation – so much so the sheer number of organizations with a cloud solution outpace or far outnumbers the ones that don't. But there is one area that has still not made the switch to the cloud, most often the security department. But the advent of using vid...
While the foundation of autonomous retail has been built up over the past few years, it is only now that retailers are beginning to fully experiment with the technology. There were an estimated 350 stores globally in 2018 offering a fully autonomous checkout process, yet this number is forecast to increase dramatically with 10,000 stores anticipated by 2024. This acceleration in the growth of unmanned retail stores has, in part, been boosted by the COVID-19 pandemic and a demand for a more cont...