Scott Lundgren

Scott Lundgren
Chief Technology Officer, Carbon Black, Inc.Scott Lundgren is a Chief Technology Officer at Carbon Black, Inc. Previously Scott Lundgren was an Executive Director at ManTech International.
News mentions
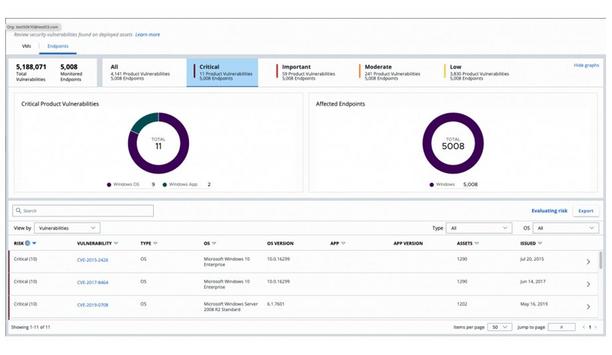
Security and IT teams have recently been facing a tidal wave of highly publicized breaches stemming from unpatched vulnerabilities, such as the attacks originating from a zero-day Windows printer spoo...
Carbon Black, a provider of next-generation endpoint security delivered via the cloud, announces that it delivered zero delayed detections and zero tainted detections in the MITRE Corporation’s...