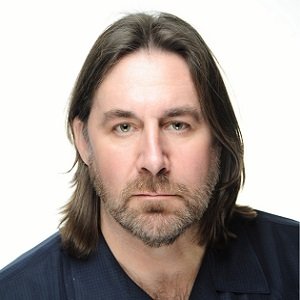
Michael Troiani

Michael Troiani
Service Manager, Idesco CorporationNews mentions
Idesco partners with Viakoo to help customers eliminate missing video & keep an eye on their facility at all times Idesco Corp., a leading New York-based security systems integr...
Readily available security technology can help officials take control of their campuses Two top priorities for school security are the ability to communicate within a facility, and...
Cloud-based computing is here and is heavily marketed as a revolution in the security industry Dealers and integrators still have questions about cloud-based services, so we asked S...